recently demonstrated a new kind of malware that could be used to
covertly steal highly sensitive data from air-gapped and
audio-gapped systems using a novel acoustic quirk in power supply
units that come with modern computing devices.
Dubbed ‘POWER-SUPPLaY[1],’ the latest research
builds on a series of
techniques[2] leveraging
electromagnetic, acoustic, thermal, optical covert channels, and
even power cables to
exfiltrate data[3]
from non-networked computers.
“Our developed malware can exploit the computer power supply unit
(PSU) to play sounds and use it as an out-of-band, secondary
speaker with limited capabilities,” Dr. Mordechai Guri outlined in
a paper published today.
[4]
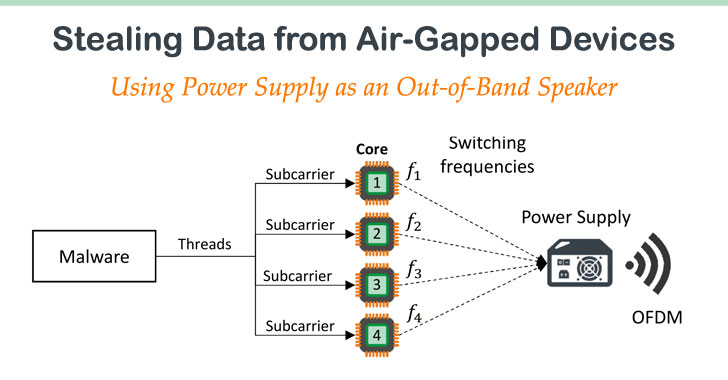
“The malicious code manipulates the internal switching frequency of
the power supply and hence controls the sound waveforms generated
from its capacitors and transformers.”
“We show that our technique works with various types of systems:
PC workstations and servers, as well as embedded systems and IoT
devices that have no audio hardware. Binary data can be modulated
and transmitted out via the acoustic signals.”
Using Power Supply as an Out-of-Band Speaker
Air-gapped systems
are considered a necessity in environments where sensitive data is
involved in an attempt to reduce the risk of data leakage. The
devices typically have their audio hardware disabled so as to
prevent adversaries from leveraging the built-in speakers and
microphones to pilfer information via sonic and
ultrasonic waves.
It also necessitates that both the transmitting and receiving
machines be located in close physical proximity to one another and
that they are infected with the appropriate malware to establish
the communication link, such as through social engineering
campaigns that exploit the target device’s vulnerabilities.
POWER-SUPPLaY functions in the same way in that the malware running
on a PC can take advantage of its PSU and use it as an out-of-band
speaker, thus obviating the need for specialized audio hardware.
“This technique enables playing audio streams from a computer
even when audio hardware is disabled, and speakers are not
present,” the researcher said. “Binary data can be modulated and
transmitted out via the acoustic signals. The acoustic signals can
then be intercepted by a nearby receiver (e.g., a smartphone),
which demodulates and decodes the data and sends it to the attacker
via the Internet.”
Put differently, the air-gap malware regulates the workload of
modern CPUs to control its power consumption and the switching
frequency of the PSU to emit an acoustic signal in the range of
0-24kHz and modulate binary data over it.
Air-Gap Bypass and Cross-Device Tracking
The malware in the compromised computer, then, not only amasses
sensitive data (files, URLs, keystrokes, encryption keys, etc.), it
also transmits data in WAV format using the acoustic sound waves
emitted from the computer’s power supply, which is decoded by the
receiver — in this case, an app running on an Android smartphone.
According to the researcher, an attacker can exfiltrate data
from audio-gapped systems to the nearby phone located 2.5 meters
away with a maximal bit rate of 50 bit/sec.
One privacy-breaking consequence of this attack is cross-device
tracking, as this technique enables the malware to capture
browsing history on the compromised system and broadcast the
information to the receiver.
As a countermeasure, the researcher suggest zoning sensitive
systems in restricted areas where mobile phones and other
electronic equipment are banned. Having an intrusion detection
system to monitor suspicious CPU behavior, and setting up
hardware-based signal detectors and jammers could also help defend
against the proposed covert channel.
With air-gapped nuclear facilities
in Iran and India[8] the target of
security breaches, the new research is yet another reminder that
complex supply chain attacks can be directed against isolated
systems.
“The POWER-SUPPLaY code can operate from an ordinary user-mode
process and doesn’t need hardware access or root-privileges,” the
researcher concluded. “This proposed method doesn’t invoke special
system calls or access hardware resources, and hence is highly
evasive.”
References
- ^
POWER-SUPPLaY
(arxiv.org) - ^
series of techniques
(cyber.bgu.ac.il) - ^
power cables to exfiltrate data
(thehackernews.com) - ^
power supply unit
(en.wikipedia.org) - ^
Air-gapped systems
(en.wikipedia.org) - ^
sonic and ultrasonic waves
(thehackernews.com) - ^
cross-device tracking
(thehackernews.com) - ^
nuclear facilities in Iran and
India (thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/rxbVwJaSMNE/air-gap-malware-power-speaker.html