New evidence amidst the ongoing probe into the espionage campaign[1]
targeting SolarWinds has uncovered an unsuccessful attempt to
compromise cybersecurity firm Crowdstrike and access the company’s
email.
The hacking endeavor was reported to the company by Microsoft’s
Threat Intelligence Center on December 15, which identified a
third-party reseller’s Microsoft Azure account to be making
“abnormal calls” to Microsoft cloud APIs during a 17-hour period
several months ago.
The undisclosed affected reseller’s Azure account handles
Microsoft Office licensing for its Azure customers, including
CrowdStrike.
Although there was an attempt by unidentified threat actors to
read email, it was ultimately foiled as the firm does not use
Microsoft’s Office 365 email service, CrowdStrike said[2].
The incident comes in the wake of the supply chain attack[3]
of SolarWinds revealed earlier this month, resulting in the
deployment of a covert backdoor (aka “Sunburst”) via malicious
updates of a network monitoring software called SolarWinds
Orion.
Since the disclosure, Microsoft[4], Cisco, VMware, Intel,
NVIDIA, and a number of US government agencies have confirmed
finding tainted Orion installations in their environments.
The development comes a week after the Windows maker, itself a
SolarWinds customer, denied hackers had infiltrated its production
systems to stage further attacks against its users and found
evidence of a separate hacking group[5]
abusing Orion software to install a separate backdoor called
“Supernova.”
It also coincides with a new report[6]
from The Washington Post today, which alleges Russian government
hackers have breached Microsoft cloud customers and stolen emails
from at least one private-sector company by taking advantage of a
Microsoft reseller that manages cloud-access services.
We have reached out to Microsoft, and we will update the story
if we hear back.
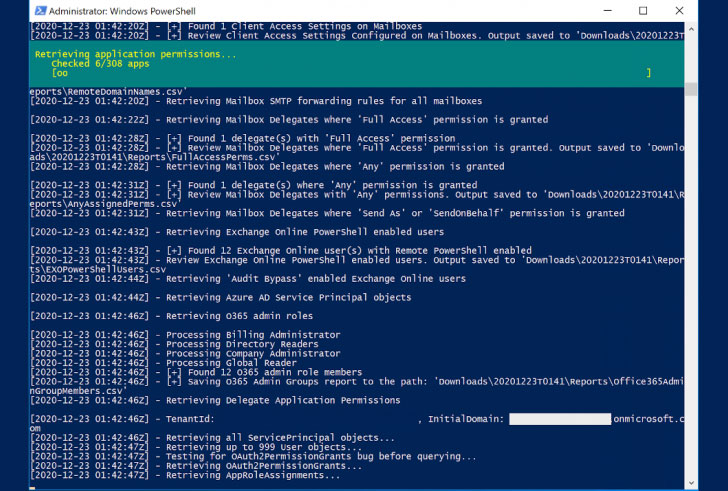
CrowdStrike has also released CrowdStrike Reporting Tool for
Azure (CRT[7]), a free tool that aims
to help organizations review excessive permissions in their Azure
Active Directory or Office 365 environments and help determine
configuration weaknesses.
In addition, the US Cybersecurity Infrastructure and Security
Agency (CISA) has separately created a similar open-source utility
called Sparrow[8]
to help detect possible compromised accounts and applications in
Azure or Office 365 environments.
“The tool is intended for use by incident responders and is
narrowly focused on activity that is endemic to the recent
identity- and authentication-based attacks seen in multiple
sectors,” CISA said[9].
For its part, SolarWinds has updated its security advisory[10], urging customers to
update Orion Platform software to version 2020.2.1 HF 2 or 2019.4
HF 6 to mitigate the risks associated with Sunburst and Supernova
vulnerabilities.
References
- ^
espionage campaign
(thehackernews.com) - ^
said
(www.crowdstrike.com) - ^
supply
chain attack (thehackernews.com) - ^
Microsoft
(thehackernews.com) - ^
separate
hacking group (thehackernews.com) - ^
new
report (www.washingtonpost.com) - ^
CRT
(github.com) - ^
Sparrow
(github.com) - ^
said
(us-cert.cisa.gov) - ^
security advisory
(www.solarwinds.com)