Weaknesses in e-commerce portals are being exploited to deploy a
Linux backdoor as well as a credit card skimmer that’s capable of
stealing payment information from compromised websites.
“The attacker started with automated e-commerce attack probes,
testing for dozens of weaknesses in common online store platforms,”
researchers from Sansec Threat Research said[1]
in an analysis. “After a day and a half, the attacker found a file
upload vulnerability in one of the store’s plugins.” The name of
the affected vendor was not revealed.
The initial foothold was then leveraged to upload a malicious
web shell and alter the server code to siphon customer data.
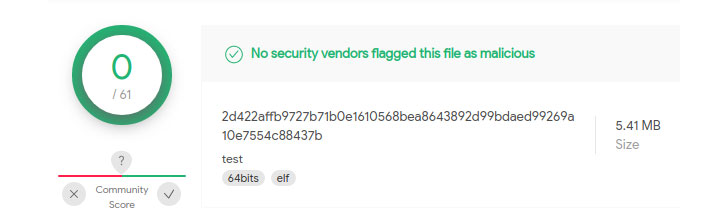
Additionally, the attacker delivered a Golang-based malware called
“linux_avp[2]” that serves as a
backdoor to execute commands remotely sent from a
command-and-control server hosted in Beijing.
Upon execution, the program is designed to remove itself from
the disk and camouflage as a “ps -ef[3]” process, which is a
utility for displaying currently-running processes in Unix and
Unix-like operating systems.
The Dutch cybersecurity firm said it also discovered a PHP-coded
web skimmer that’s disguised as a favicon image[4]
(“favicon_absolute_top.jpg”) and added to the e-commerce platform’s
code with the goal of injecting fraudulent payment forms and
stealing credit card information entered by customers in real-time,
before transmitting them to a remote server.
Furthermore, Sansec researchers said the PHP code was hosted on
a server located in Hong Kong and that it was previously used as a
“skimming exfiltration endpoint in July and August of this
year.”
References
Read more https://thehackernews.com/2021/11/new-golang-based-linux-malware.html