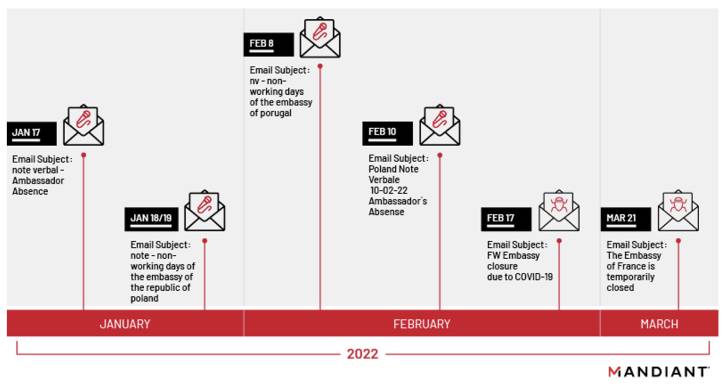
A Russian state-sponsored threat actor has been observed
targeting diplomatic and government entities as part of a series of
phishing campaigns commencing on January 17, 2022.
Threat intelligence and incident response firm Mandiant
attributed the attacks to a hacking group tracked as APT29 (aka
Cozy Bear), with some set of the activities associated with the
crew assigned the moniker Nobelium[1]
(aka UNC2452/2652).
“This latest wave of spear phishing showcases APT29’s enduring
interests in obtaining diplomatic and foreign policy information
from governments around the world,” the Mandiant said[2]
in a report published last week.
The initial access is said to have been aided through
spear-phishing emails masquerading as administrative notices, using
legitimate but compromised email addresses from other diplomatic
entities.
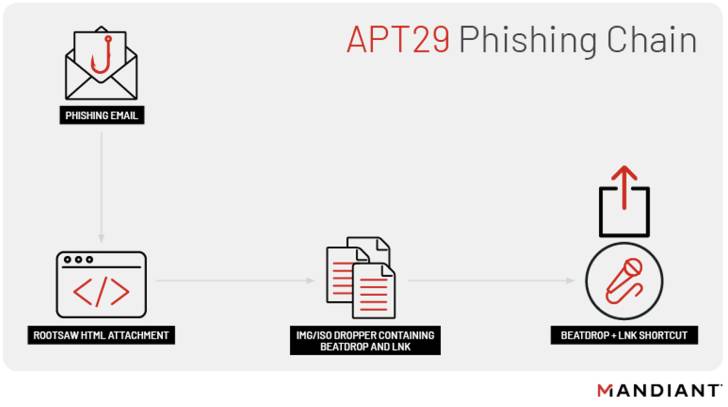
These emails contain an HTML dropper attachment called ROOTSAW
(aka EnvyScout[3]) that, when opened,
triggers an infection sequence that delivers and executes a
downloader dubbed BEATDROP on a target system.
Written in C, BEATDROP is designed to retrieve next-stage
malware from a remote command-and-control (C2) server. It achieves
this by abusing Atlassian’s Trello service to store victim
information and fetch AES-encrypted shellcode payloads to be
executed.
Also employed by APT29 is a tool named BOOMMIC (aka VaporRage[4]) to establish a foothold
within the environment, followed by escalating their privileges
within the compromised network for lateral movement and extensive
reconnaissance of hosts.
What’s more, a subsequent operational shift observed in February
2022 saw the threat actor pivoting away from BEATDROP in favor of a
C++-based loader referred to as BEACON, potentially reflecting the
group’s ability to periodically alter their TTPs to stay under the
radar.
BEACON, programmed in C or C++, is part of the Cobalt Strike
framework that facilitates arbitrary command execution, file
transfer, and other backdoor functions such as capturing
screenshots and keylogging.
The development follows the cybersecurity company’s decision[5]
to merge the uncategorized cluster UNC2452 into APT29, while noting
the highly sophisticated group’s propensity for evolving and
refining its technical tradecraft to obfuscate activity and limit
its digital footprint to avoid detection.
Nobelium, notably, breached multiple enterprises by means of a
supply chain attack in which the adversary accessed and tampered
with SolarWinds source code, and used the vendor’s legitimate
software updates to spread the malware to customer systems.
“The consistent and steady advancement in TTPs speaks to its
disciplined nature and commitment to stealthy operations and
persistence,” Mandiant said, characterizing APT29 as an “evolving,
disciplined, and highly skilled threat actor that operates with a
heightened level of operational security (OPSEC) for the purposes
of intelligence collection.”
The findings also coincide with a special report[6]
from Microsoft, which observed Nobelium attempting to breach IT
firms serving government customers in NATO member states, using the
access to siphon data from Western foreign policy
organizations.
References
Read more https://thehackernews.com/2022/05/russian-hackers-targeting-diplomatic.html