An unknown advanced persistent threat (APT) group has been
linked to a series of spear-phishing attacks targeting Russian
government entities since the onset of the Russo-Ukrainian war in
late February 2022.
“The campaigns […] are designed to implant a Remote Access
Trojan (RAT) that can be used to surveil the computers it infects,
and run commands on them remotely,” Malwarebytes said[1]
in a technical report published Tuesday.
The cybersecurity company attributed the attacks with low
confidence to a Chinese hacking group, citing infrastructure
overlaps between the RAT and Sakula Rat malware used by a threat
actor known as Deep Panda[2].
The attack chains, while leveraging different lures over the
course of two months, all employed the same malware barring small
differences in the source code.
The campaign is said to have commenced around February 26, days
after Russia’s military invasion of Ukraine, with the emails
distributing the RAT under the guise of an interactive map of
Ukraine (“interactive_map_UA.exe”).
The development once again demonstrates threat actors’
capabilities to adapt and adjust their attacks to world events,
using the most relevant and up-to-date lures to maximize their
chances of success.
A second early March attack wave primarily targeted the
state-controlled RT TV and involved the use of a rogue software fix
for the Log4Shell vulnerability[3]
that made headlines in late 2021.
Besides including the patch in the form of a compressed TAR
file, the email message also came with a PDF document with
instructions to install the patch and listed the best security
practices to follow, including enabling two-factor authentication,
using Kaspersky antivirus, and refraining from opening or replying
to suspicious emails.
In a further attempt to boost the authenticity of the email, the
document also contained a VirusTotal URL[4]
pointing to an unrelated file to give the impression that the Log4j
patch file is not malicious.
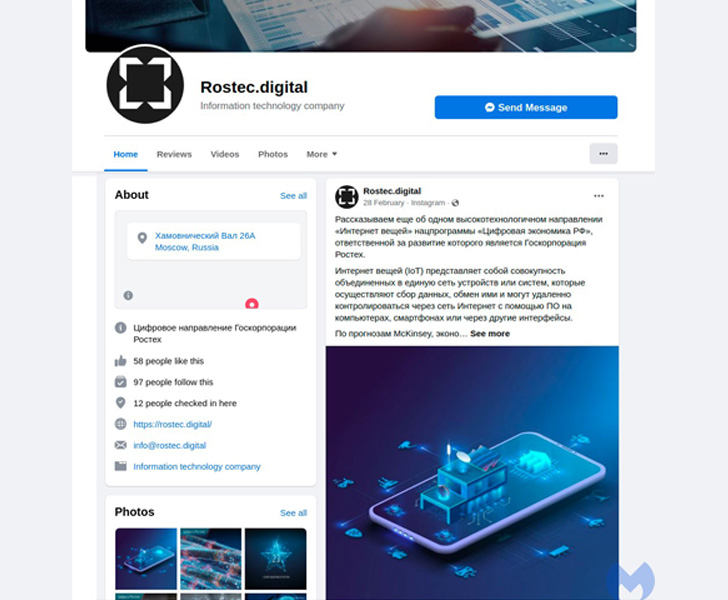
What’s more, the email featured links to an attacker-controlled
domain “rostec[.]digital” along with fraudulent profiles created on
Facebook and Instagram alluding to the Russian defense
conglomerate.
“Interestingly, the threat actor created the Facebook page in
June 2021, nine months before it was used in this campaign,” the
researchers said. “This was probably an attempt to attract
followers, to make the page look more legitimate, and it suggests
the APT group were planning this campaign long before the invasion
of Ukraine.”
The third iteration of the attack that followed made use of
another malicious executable file — this time “build_rosteh4.exe” —
in an attempt to pass off the malware as though it’s from
Rostec.
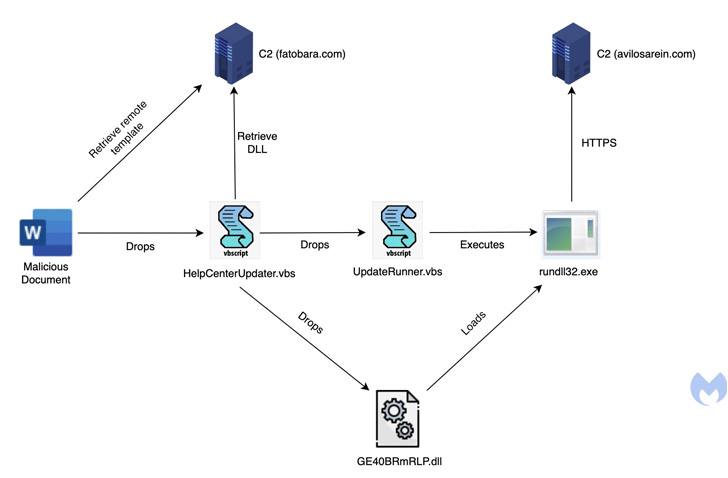
Lastly, in mid-April 2022, the attackers pivoted to a job-themed
phishing bait for Saudi Aramco, a Saudi Arabian petroleum and
natural gas company, the weaponized Microsoft Word document acting
as a trigger for an infection sequence to deploy the RAT.
The DLL payload employs a variety of advanced tricks to thwart
analysis, including control flow flattening and string obfuscation,
while also incorporating features that allow it to arbitrary files
sent from a remote server to the infected host and execute
command-line instructions.
The findings closely follow findings from Check Point that a
Chinese adversarial collective[5] with connections to
Stone Panda and Mustang Panda targeted at least two research
institutes located in Russia with a previously undocumented
backdoor called Spinner.
References
- ^
said
(blog.malwarebytes.com) - ^
Deep
Panda (thehackernews.com) - ^
Log4Shell vulnerability
(thehackernews.com) - ^
VirusTotal URL
(www.virustotal.com) - ^
Chinese
adversarial collective (thehackernews.com)
Read more https://thehackernews.com/2022/05/researchers-find-new-malware-attacks.html