A sophisticated scam-as-a-service operation dubbed
Classiscam has now infiltrated into Singapore, more than 1.5
years after expanding to Europe[1].
“Scammers posing as legitimate buyers approach sellers with the
request to purchase goods from their listings and the ultimate aim
of stealing payment data,” Group-IB said[2]
in a report shared with The Hacker News.
The cybersecurity firm called the operators a “well-coordinated
and technologically advanced scammer criminal network.”
Classiscam refers to a Russia-based
cybercrime operation[3]
that was first recorded in summer 2019 but only came under
spotlight a year later coinciding with a surge in activity owing to
an increase in online shopping in the aftermath of COVID-19
outbreak.
Called the most widely used fraud scheme[4] during the pandemic,
Classiscam targets people who use marketplaces and services
relating to property rentals, hotel bookings, online bank
transfers, online retail, ride-sharing, and package deliveries.
Initial targets included users of popular Russian classifieds
and marketplaces, before migrating to Europe and the U.S. There are
believed to be over 90 active groups using Classiscam’s services to
target users in Bulgaria, the Czech Republic, France, Kazakhstan,
Kirghizia, Poland, Romania, Ukraine, the U.S. and Uzbekistan.
The fraudulent operation spans acrosss 64 countries in Europe,
the Commonwealth of Independent States (CIS), and the Middle East,
with 169 brands used to carry out the attacks. From April 2020 to
February 2022, criminals leveraging Classiscam are said to have
made at least $29.5 million in illicit profits.
What’s notable about this campaign is its heavy reliance on
Telegram bots and chats to coordinate operations and create
phishing and scam pages.
Here is the core of how it all works: The scammers post bait ads
on popular marketplaces and classified websites, usually offering
game consoles, laptops, and smartphones for sale at significant
discounts.
When a potential victim contacts the seller (i.e., the threat
actor) through the online storefront, the Classiscam operator
deceives the target into continuing the chat on a third-party
messaging service like WhatsApp or Viber before sending a link to a
rogue payment page to complete the transaction.
The scheme involves a hierarchy of administrators, workers, and
callers. While administrators are in charge of recruiting new
members, automating the creation of scam pages, and registering new
accounts, it’s the workers who create accounts on free classifieds
websites and place the decoy ads.
Workers, who receive 70-80% of the stolen sums, are also
responsible for communicating with the victims through the
platform’s chat systems and sending phishing links designed to make
payments for the purchased goods.
“Workers are key participants of the Classiscam scam scheme:
their goal is to attract traffic to phishing resources,” the
researchers said.
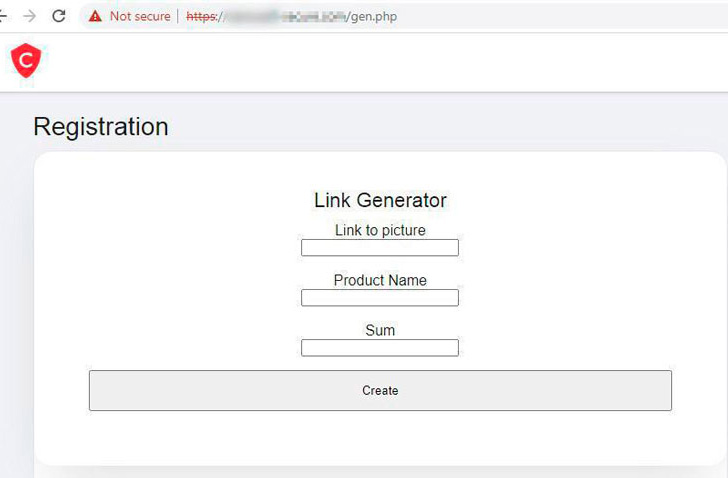
The phishing URLs, for their part, are generated through
Telegram bots that mimic the payment pages of the local classified
websites but are hosted on lookalike domains. This however
necessitates that the workers send the link with the bait product
to the bot.
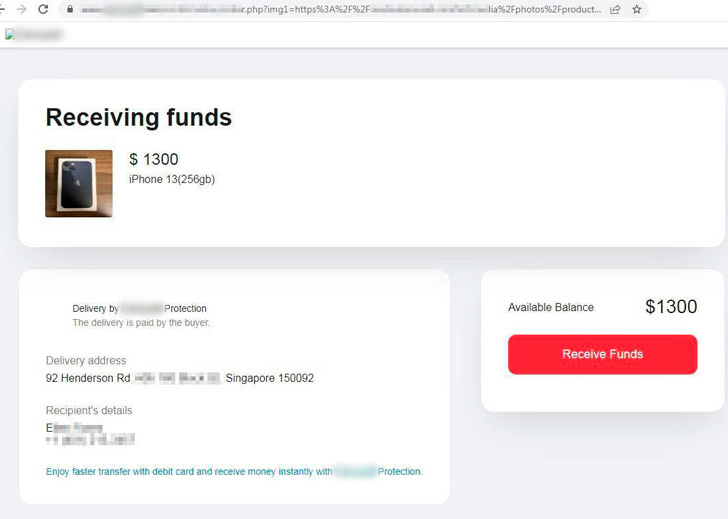
“After initial contact with the legitimate seller, the scammers
generate a unique phishing link that confuses the sellers by
displaying the information about the seller’s offer and imitating
the official classified’s website and URL,” the researchers said.
“Scammers claim that payment has been made and lure the victim into
either making a payment for delivery or collecting the
payment.”
The phishing pages also include an option to check the victim’s
bank account balance with the goal of identifying the most
“valuable” cards.
What’s more, some cases incorporate an attempt to trick the
victims a second time by calling them to request for a refund in
order to receive their money back. These calls are made by
assistant workers who masquerade as tech support specialists for
the platform.
In this scenario, the targets are taken to a fraudulent payment
page to enter their card details and confirm it by providing a
password received via SMS. But instead of a refund, the same amount
is debited from the victim’s card again.
While the aforementioned modus operandi is an instance of seller
scam, wherein a buyer (i.e., victim) receives a phishing payment
link and is defrauded of their money, there also exists buyer
scams.
This entails a fraudster contacting a legitimate seller under
the guise of a customer and sending a bot-generated fake payment
form impersonating a marketplace allegedly for verification
purposes. But once the seller enters their bank card information,
an amount equivalent to the product’s cost is deducted from their
account.
The entire attack infrastructure operated by Classiscammers
comprises 200 domains, 18 of which were created to trick the users
of an unnamed Singaporean classified website. Other sites in the
network pose as Singaporean moving companies, European, Asian, and
Middle Eastern classified websites, banks, marketplaces, food and
crypto brands, and delivery companies.
“As it sounds, Classiscam is far more complex to tackle than the
conventional types of scams,” Group-IB’s Ilia Rozhnov siad. “Unlike
the conventional scams, Classiscam is fully automated and could be
widely distributed. Scammers could create an inexhaustible list of
links on the fly.”
“To complicate the detection and takedown, the home page of the
rogue domains always redirects to the official website of a local
classified platform.”
References
- ^
expanding to Europe
(www.group-ib.com) - ^
said
(www.group-ib.com) - ^
Russia-based cybercrime operation
(blog.group-ib.com) - ^
most
widely used fraud scheme (www.group-ib.com)
Read more https://thehackernews.com/2022/08/researchers-uncover-classiscam-scam-as.html