Threat actors associated with the Cuba ransomware have been
linked to previously undocumented tactics, techniques and
procedures (TTPs), including a new remote access trojan called
ROMCOM RAT on compromised systems.
The new findings[1]
come from Palo Alto Networks’ Unit 42 threat intelligence team,
which is tracking the double extortion ransomware group under the
constellation-themed moniker[2] Tropical
Scorpius.
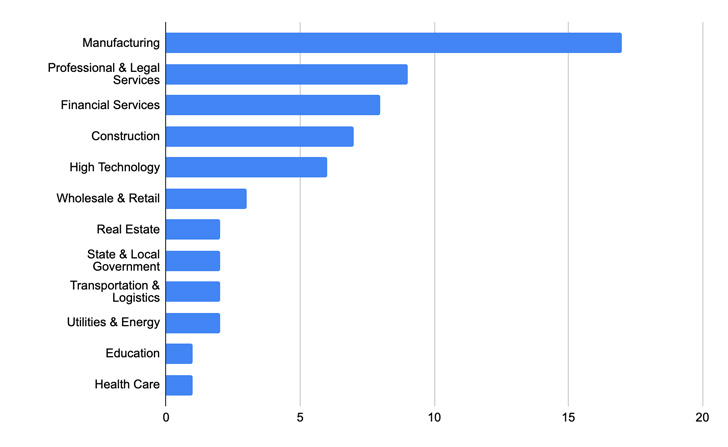
Cuba ransomware (aka COLDDRAW[3]), which was first
detected in December 2019, reemerged on the threat landscape in
November 2021 and has been attributed to attacks against 60
entities in five critical infrastructure sectors, amassing at least
$43.9 million in ransom payments.
Of the 60 victims listed on its data leak site, 40 are located
in the U.S., indicating a not as global distribution of targeted
organizations as other ransomware gangs.
“Cuba ransomware is distributed through Hancitor malware, a
loader known for dropping or executing stealers, such as Remote
Access Trojans (RATs) and other types of ransomware, onto victims’
networks,” according to a December 2021 alert[4]
from the U.S. Federal Bureau of Investigation (FBI).
“Hancitor malware actors use phishing emails, Microsoft Exchange
vulnerabilities, compromised credentials, or legitimate Remote
Desktop Protocol (RDP) tools to gain initial access to a victim’s
network.”
In the intervening months, the ransomware operation has received
an upgrade with an aim to “optimize its execution, minimize
unintended system behavior, and provide technical support to the
ransomware victims if they choose to negotiate,” per Trend
Micro.
Chief among the changes encompassed terminating more processes
before encryption (viz Microsoft Outlook, Exchange, and MySQL),
expanding the file types to be excluded, and revision to its ransom
note to offer victim support via quTox.
Tropical Scorpius is also believed to share connections with a
data extortion marketplace called Industrial Spy, as reported[5]
by Bleeping Computer in May 2022, with the exfiltrated data
following a Cuba ransomware attack posted for sale on the illicit
portal instead of its own data leak site.
The latest updates observed by Unit 42 in May 2022 has to do
with the defense evasion tactics employed prior to the deployment
of the ransomware to fly under the radar and move laterally across
the compromised IT environment.
“Tropical Scorpius leveraged a dropper that writes a kernel
driver to the file system called ApcHelper.sys,” the company noted.
“This targets and terminates security products. The dropper was not
signed, however, the kernel driver was signed using the certificate
found in the LAPSUS$ NVIDIA leak[6].”
The main task of the kernel driver is to terminate processes
associated with security products so as to bypass detection. Also
incorporated in the attack chain is a local privilege escalation
tool downloaded from a remote server to gain SYSTEM
permissions.
This, in turn, is achieved by triggering an exploit for
CVE-2022-24521 (CVSS score: 7.8), a flaw in the Windows Common Log
File System (CLFS) that was patched[7]
by Microsoft as a zero-day flaw in April 2022.
The privilege escalation step is followed by carrying out system
reconnaissance and lateral movement activities through tools like
ADFind and Net Scan, while also using a ZeroLogon utility that
exploits CVE-2020-1472[8]
to gain domain administrator rights.
Furthermore, the intrusion paves the way for the deployment of a
novel backdoor called ROMCOM RAT, which is equipped to start a
reverse shell, delete arbitrary files, upload data to a remote
server, and harvest a list of running processes.
The remote access trojan, per Unit 42, is said to be under
active development, as the cybersecurity firm discovered a second
sample uploaded to the VirusTotal database on June 20, 2022.
The improved variant comes with support for a broadened set of
22 commands, counting the ability to download bespoke payloads to
capture screenshots as well as extract a list of all installed
applications to send back to the remote server.
“Tropical Scorpius remains an active threat,” the researchers
said. “The group’s activity makes it clear that an approach to
tradecraft using a hybrid of more nuanced tools focusing on
low-level Windows internals for defense evasion and local privilege
escalation can be highly effective during an intrusion.
The findings come as emerging ransomware groups such as Stormous[9], Vice Society[10], Luna[11], SolidBit[12], and BlueSky are
continuing to proliferate and evolve in the cybercrime ecosystem,
at the same using advanced encryption techniques and delivery
mechanisms.
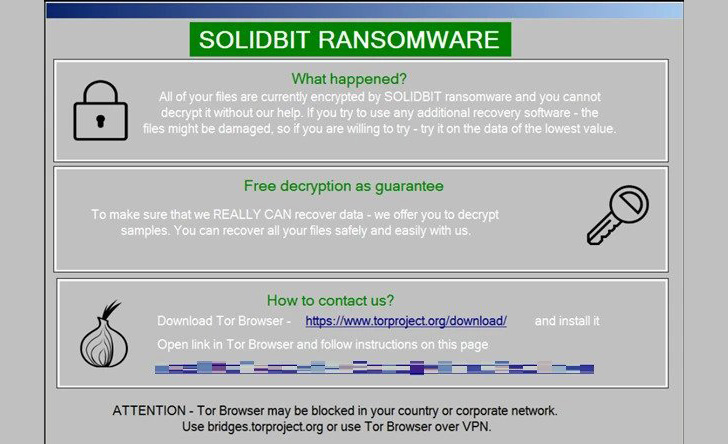
SolidBit stands out for its targeting of users of popular video
games and social media platforms by masquerading as different
applications like a League of Legends account checker tool and
tools like Social Hacker and Instagram Follower Bot, allowing the
actors to cast a wide net of potential victims.
“SolidBit ransomware is compiled using .NET and is actually a
variant of Yashma[13] ransomware, also known
as Chaos,” Trend Micro noted[14] in a write-up last
week.
“It’s possible that SolidBit’s ransomware actors are currently
working with the original developer of Yashma ransomware and likely
modified some features from the Chaos builder, later rebranding it
as SolidBit.”
BlueSky, for its part, is known to utilize multithreading to
encrypt files on the host for faster encryption, not to mention
adopt anti-analysis techniques to obfuscate its appearance.
The ransomware payload, which kicks off with the execution of a
PowerShell script retrieved from an attacker-controlled server,
also disguises itself as a legitimate Windows application
(“javaw.exe”).
“Ransomware authors are adopting modern advanced techniques such
as encoding and encrypting malicious samples, or using multi-staged
ransomware delivery and loading, to evade security defenses,” Unit
42 noted[15].
“BlueSky ransomware is capable of encrypting files on victim
hosts at rapid speeds with multithreaded computation. In addition,
the ransomware adopts obfuscation techniques, such as API hashing,
to slow down the reverse engineering process for the analyst.”
References
- ^
new
findings (unit42.paloaltonetworks.com) - ^
constellation-themed moniker
(unit42.paloaltonetworks.com) - ^
COLDDRAW
(www.mandiant.com) - ^
December
2021 alert (www.ic3.gov) - ^
reported
(www.bleepingcomputer.com) - ^
LAPSUS$
NVIDIA leak (thehackernews.com) - ^
patched
(thehackernews.com) - ^
CVE-2020-1472
(thehackernews.com) - ^
Stormous
(cloudsek.com) - ^
Vice
Society (blog.sekoia.io) - ^
Luna
(thehackernews.com) - ^
SolidBit
(medium.com) - ^
Yashma
(thehackernews.com) - ^
noted
(www.trendmicro.com) - ^
noted
(unit42.paloaltonetworks.com)
Read more https://thehackernews.com/2022/08/hackers-behind-cuba-ransomware-attacks.html