So far 2022 confirms that passwords are not dead yet. Neither
will they be anytime soon. Even though Microsoft and Apple are
championing passwordless authentication methods, most applications
and websites will not remove this option for a very long time.
Think about it, internal apps that you do not want to integrate
with third-party identity providers, government services, legacy
applications, and even SaaS providers may not want to invest in new
integrations or restrict their existing authentication methods.
After all, online businesses are interested in user traction, and
security usually brings friction. For example, a few days ago,
Kickstarter sent out millions of password
reset[1] emails “simplifying its
login process,” including for people that used social login without
a password.
Though you may be able to remove passwords from many enterprise
components, a large portion of third-party providers, government
portals, business suppliers, and SaaS services will still rely
primarily on password-based accounts. No wonder Gartner believes
that digital supply chain risk is one of 2022’s biggest
challenges.
So long as any part of your infrastructure or cloud footprint
uses passwords, they will ultimately become the cheap and easy
attack vector which is leading to 80% of breaches in 2022 as
well.
Why are passwords difficult to protect?
Online password usage is completely unmonitored by most
organizations. There is no obvious policy to prevent reusing
corporate LDAP (Active Directory) passwords in online services, or
sharing the same passwords across multiple web accounts. Password
managers are opt-in and rarely available or used across all
employees and accounts because it’s an overhead for productivity
for most non-IT workers.
Once important accounts’ passwords are reused in online
services, or saved and synced across browsers, there is no telling
how or where it is stored. And when they get breached, leaked
passwords will lead to account takeovers, credential stuffing,
business email compromise, and several other nasty attack
vectors.
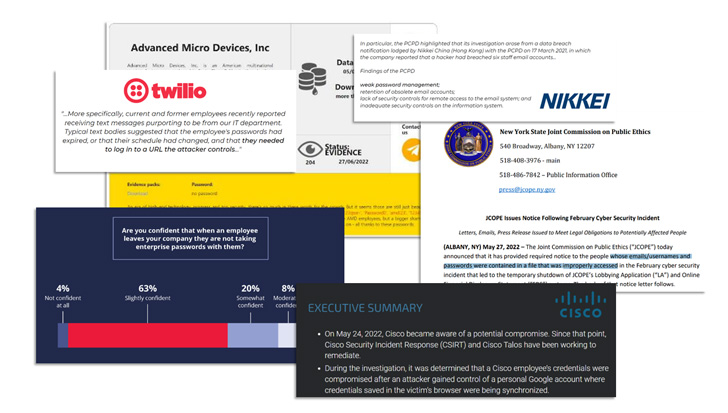
This was exactly the case recently with Cisco, which was
breached using a saved VPN password that was synced across
browsers, according to the reports. Although MFA also needed to be
compromised in the process, it only makes sense to protect all
factors involved in our authentication process.
To make things worse, with all of the public social data for
correlation, password reuse in personal accounts, (using private
emails with corporate passwords) can also be a devastating and
unmonitored vulnerability. After all, people are not too creative[2]
in coming up with their passwords.
So how to prevent password leaks and stop worrying
about password-related threats?
Fortunately, there is a cure. Most web-based accounts are
created individually and form a big part of your Shadow IT
footprint, so education must certainly be a part of it. But the
only hard solution is to rigorously check for password hygiene
across all accounts that are created and used online.
The browser is the sole point in the process of password usage,
where clear-text visibility is attainable. It is your number one
application providing the gateway to almost all internal and
external services and resources, and the largest unmonitored gap
for defending your accounts.
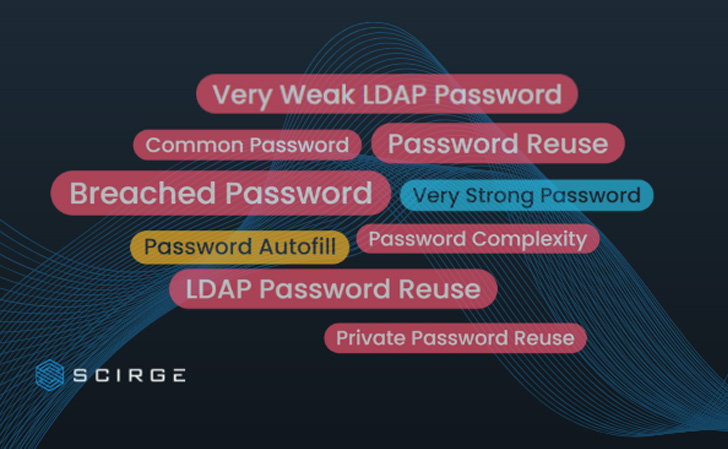
Scirge uses a
browser extension as the endpoint component[3]
that is transparent for the employees. It provides customizable
password hygiene checks without any user action. This results in
all passwords being checked for sufficient complexity and strength.
Also, their secure hash is used to compare each password for reuse,
sharing, and even against custom blacklists or known breached
passwords.
Reusing your AD/LDAP password online? Gotcha. Using your secure
corporate passwords for a private account? Scirge can see that.
Scirge allows you to monitor corporate accounts, and even
private password reuse based on granular, centrally managed
policies, without the compromise of PII data. All password hashes
and indicators are stored at your on-site server that you are 100%
in control of. Over 25 indicators reveal risky accounts and
employees with low password hygiene and allow highly targeted and
personalized educational notifications.
On top of all, Scirge creates personal inventories of all app
and account usages, providing visibility into ex-employee accounts
that they could access even after leaving. High-privilege or
service-email usage can be identified to mitigate spear phishing
attempts. Scirge can also collect browser-saved accounts, and
detect internal threats. Someone using accounts belonging to others
in the organization is immediately spotted for compliance,
segregation of duties, and other security purposes.
Curious to learn more? Click here to learn more[4], or sign-up for a free evaluation right
here[5].
References
- ^
Kickstarter sent out millions of
password reset (techcrunch.com) - ^
are not
too creative (www.thetechoutlook.com) - ^
Scirge uses a browser extension as the
endpoint component (thn.scirge.com) - ^
Click here to learn more
(thn.scirge.com) - ^
sign-up
for a free evaluation right here
(survey.scirge.com)
Read more https://thehackernews.com/2022/09/stop-worrying-about-passwords-forever.html