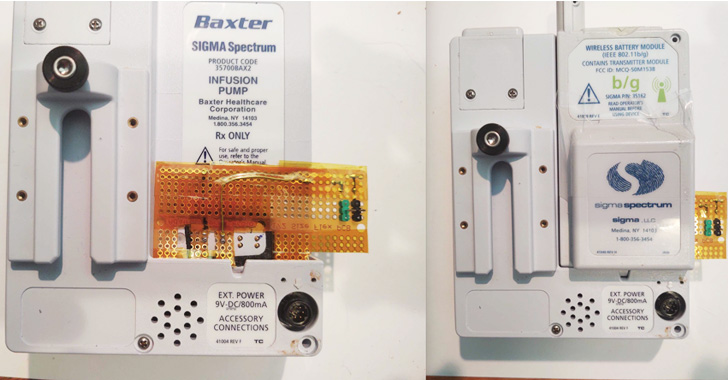
Multiple security vulnerabilities have been disclosed in
Baxter’s internet-connected infusion pumps used by healthcare
professionals in clinical environments to dispense medication to
patients.
“Successful exploitation of these vulnerabilities could result
in access to sensitive data and alteration of system
configuration,” the U.S. Cybersecurity and Infrastructure Security
Agency (CISA) said[1]
in a coordinated advisory.
Infusion pumps are internet-enabled devices used by hospitals to
deliver medication and nutrition directly into a patient’s
circulatory system.
The four vulnerabilities in question, discovered by cybersecurity firm Rapid7[2] and reported to Baxter
in April 2022, affect the following Sigma Spectrum Infusion systems
–
- Sigma Spectrum v6.x model 35700BAX
- Sigma Spectrum v8.x model 35700BAX2
- Baxter Spectrum IQ (v9.x) model 35700BAX3
- Sigma Spectrum LVP v6.x Wireless Battery Modules v16, v16D38,
v17, v17D19, v20D29 to v20D32, and v22D24 to v22D28 - Sigma Spectrum LVP v8.x Wireless Battery Modules v17, v17D19,
v20D29 to v20D32, and v22D24 to v22D28 - Baxter Spectrum IQ LVP (v9.x) with Wireless Battery Modules
v22D19 to v22D28
The list of flaws uncovered is below –
- CVE-2022-26390 (CVSS score: 4.2) – Storage of
network credentials and patient health information (PHI) in
unencrypted format - CVE-2022-26392 (CVSS score: 2.1) – A format string vulnerability[3] when running a Telnet[4] session
- CVE-2022-26393 (CVSS score: 5.0) – A format
string vulnerability when processing Wi-Fi SSID information,
and - CVE-2022-26394 (CVSS score: 5.5) – Missing
mutual authentication with the gateway server host
Successful exploitation of the above vulnerabilities could cause
a remote denial-of-service (DoS), or enable an attacker with
physical access to the device to extract sensitive information or
alternatively carry out adversary-in-the-middle attacks.
The vulnerabilities could further result in a “loss of critical
Wi-Fi password data, which could lead to greater network access
should the network not be properly segmented,” Deral Heiland,
principal security researcher for IoT at Rapid7, told The Hacker
News.
Baxter, in an advisory, emphasized that the issues only affect
customers who use the wireless capabilities of the Spectrum
Infusion System, but also cautioned it could lead to a delay or
interruption of therapy should the flaws be weaponized.
“If exploited, the vulnerabilities could result in disruption of
[Wireless Battery Module] operation, disconnection of the WBM from
the wireless network, alteration of the WBM’s configuration, or
exposure of data stored on the WBM,” the company said[5].
The latest findings are yet another indication of how common
software vulnerabilities continue to plague the medical industry, a
concerning development given their potential implications affecting
patient care.
That said, this is not the first time security flaws in infusion
pumps have come under the scanner. Earlier this March, Palo Alto
Networks Unit 42 disclosed[6]
that an overwhelming majority of infusion pumps were exposed to
nearly 40 known vulnerabilities, highlighting the need to secure
healthcare systems from security threats.
Baxter is recommending customers to ensure that all data and
settings are erased from decommissioned pumps, place infusion
systems behind a firewall, enforce network segmentation, and use
strong wireless network security protocols to prevent unauthorized
access.
It’s crucial to “implement processes and procedures to manage
the de-acquisition of medical technology, [and] to assure that PII
and/or configuration data such as Wi-Fi, WPA, PSK, etc., are purged
from the devices prior to resale or transfer to another party,”
Heiland said.
“Maintain strong physical security within and around medical
areas containing MedTech devices, as well as areas with access to a
biomed network. Implement network segmentation for all biomed
networks to prevent other general or business networks from
communicating with MedTech devices.”
References
Read more https://thehackernews.com/2022/09/new-vulnerabilities-reported-in-baxters.html