Researchers have disclosed a new offensive framework called
Manjusaka that they call a “Chinese sibling of Sliver and Cobalt
Strike.”
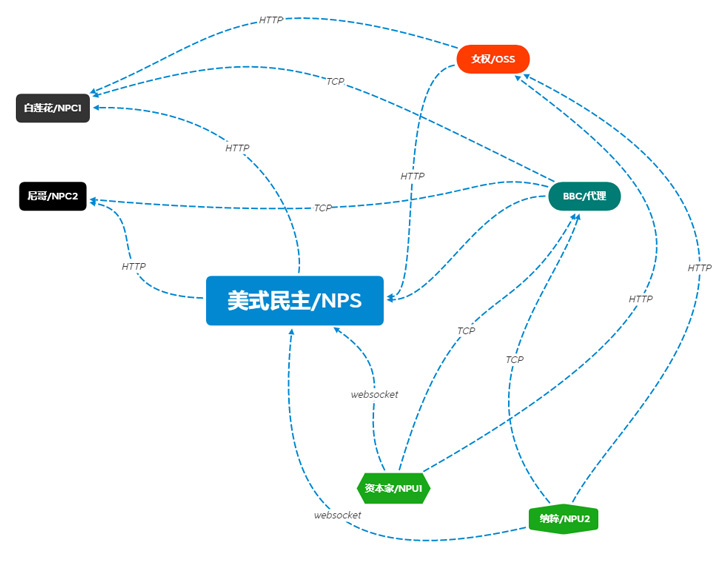
“A fully functional version of the command-and-control (C2),
written in GoLang with a User Interface in Simplified Chinese, is
freely available and can generate new implants with custom
configurations with ease, increasing the likelihood of wider
adoption of this framework by malicious actors,” Cisco Talos
said[1]
in a new report.
Sliver[2]
and Cobalt Strike[3]
are legitimate adversary emulation frameworks that have been used
by threat actors to carry out post-exploitation activities such as
network reconnaissance, lateral movement, and facilitating the
deployment of follow-on payloads.
Written in Rust, Manjusaka — meaning “cow flower” — is
advertised as an equivalent to the Cobalt Strike framework with
capabilities to target both Windows and Linux operating systems.
Its developer is believed to be located in the GuangDong region of
China.
“The implant consists of a multitude of remote access trojan
(RAT) capabilities that include some standard functionality and a
dedicated file management module,” the researchers noted.
Some of the supported features involve executing arbitrary
commands, harvesting browser credentials from Google Chrome,
Microsoft Edge, Qihoo 360, Tencent QQ Browser, Opera, Brave, and
Vivaldi, gathering Wi-Fi passwords, capturing screenshots, and
obtaining comprehensive system information.
It’s also designed to launch the file management module to carry
out a wide range of activities such as enumerating files as well as
managing files and directories on the compromised system.
On the other hand, the ELF variant of the backdoor, while
including most of the functionalities as its Windows counterpart,
doesn’t incorporate the ability to collect credentials from
Chromium-based browsers and harvest Wi-Fi login passwords.
Also, part of the Chinese language framework is a C2 server
executable that’s coded in Golang and is available on GitHub at
“hxxps://github[.]com/YDHCUI/manjusaka.” A third component is an
admin panel built on the Gin web framework[4]
that enables an operator to create the Rust implant.
The server binary, for its part, is engineered to monitor and
administer an infected endpoint, in addition to generating the
appropriate Rust implants depending on the operating system and
issuing the necessary commands.
That said, the chain of evidence suggests that it’s either under
active development or its components are offered to other actors as
a service.
Talos said it made the discovery during its investigation of a
maldoc infection chain that leverages COVID-19-themed lures in
China to deliver Cobalt Strike beacons on infected systems, adding
the same threat actor also used the implants from the Manjusaka
framework in the wild.
The findings arrive weeks after it emerged that malicious actors
have been observed abusing another legitimate adversary simulation
software called Brute Ratel[5]
(BRc4) in their attacks in an attempt to stay under the radar and
evade detection.
“The availability of the Manjusaka offensive framework is an
indication of the popularity of widely available offensive
technologies with both crimeware and APT operators,” the
researchers said.
“This new attack framework contains all the features that one
would expect from an implant, however, it is written in the most
modern and portable programming languages. The developer of the
framework can easily integrate new target platforms like MacOSX or
more exotic flavors of Linux as the ones running on embedded
devices.”
References
- ^
said
(blog.talosintelligence.com) - ^
Sliver
(github.com) - ^
Cobalt
Strike (www.cobaltstrike.com) - ^
Gin web framework
(github.com) - ^
Brute
Ratel (thehackernews.com)
Read more https://thehackernews.com/2022/08/chinese-hackers-using-new-manjusaka.html