As threat complexity increases and the boundaries of an
organization have all but disappeared, security teams are more
challenged than ever to deliver consistent security outcomes. One
company aiming to help security teams meet this challenge is
Stellar Cyber[1].
Stellar Cyber claims to address the needs of MSSPs by providing
capabilities typically found in NG-SIEM, NDR, and SOAR products in
their Open XDR platform, managed with a single license. According
to Stellar Cyber, this consolidation means faster security analyst
ramp time and customer onboarding with far less manually intensive
tasks required. Stellar Cyber currently counts 20+ of the top MSSP
providers as customers, providing security for over 3 million
assets. In addition, stellar Cyber claims after deployment, users
see up to 20x faster mean time to respond (MTTR), a bold claim.
We recently took a closer look at the Stellar Cyber Security
Operations Platform.
Before we begin
Before digging into the platform, here are a few things MSSPs
should know about Stellar Cyber:
- Works with any EDR: Stellar Cyber could be
classified as an Open XDR as it delivers visibility across your
customer’s environments; however, it is not an extension of an EDR
product. Conversely, Stellar Cyber offers pre-built integrations to
any major EDR vendors meaning your customers can use whatever EDR
they want if you use Stellar Cyber.
- It’s Multi-Tenant: Stellar Cyber is a
multi-tenant solution meaning that your customer’s data will not be
commingled, enabling you to offer your services in regions
specifically concerned about data privacy. Further, this
multi-tenancy approach can drive better analyst-to-customer ratios.
In certain situations, work done for one customer can be applied to
another with zero loss of data integrity.
To facilitate this product review, the team at Stellar Cyber
gave us access to the cloud-based version of their product, so
after a brief product walkthrough delivered by a Stellar Cyber
support person, we logged into the product.
Responding to an Incident from the Home
page
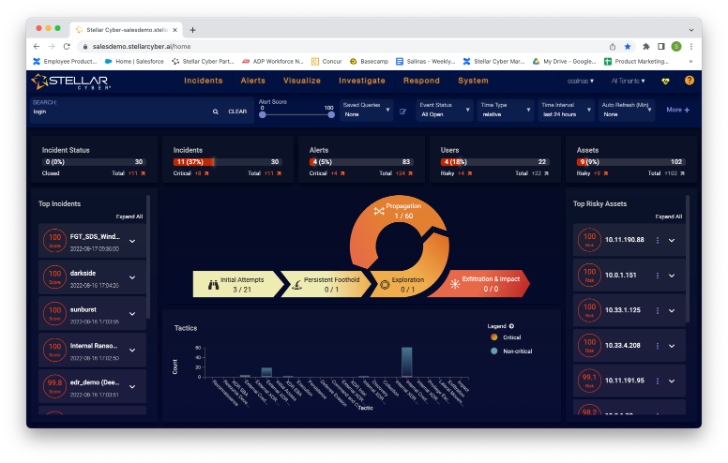
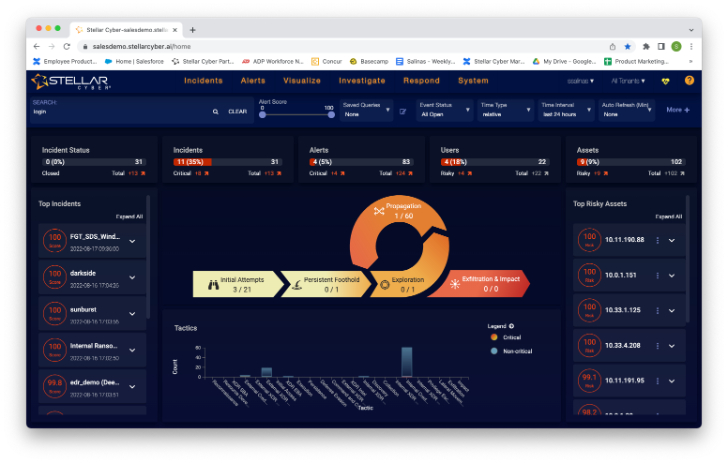
This is the initial screen you see when logging into Stellar
Cyber. You would expect to see many elements on the analyst home
screen, such as top incidents and riskiest assets. An interesting
piece on this screen is what Stellar Cyber calls the Open XDR Kill
Chain. By clicking on any segment of the kill chain, you can access
the threats associated with that portion of the attack chain. For
example, I clicked on “Initial Attempts” to access this screen.
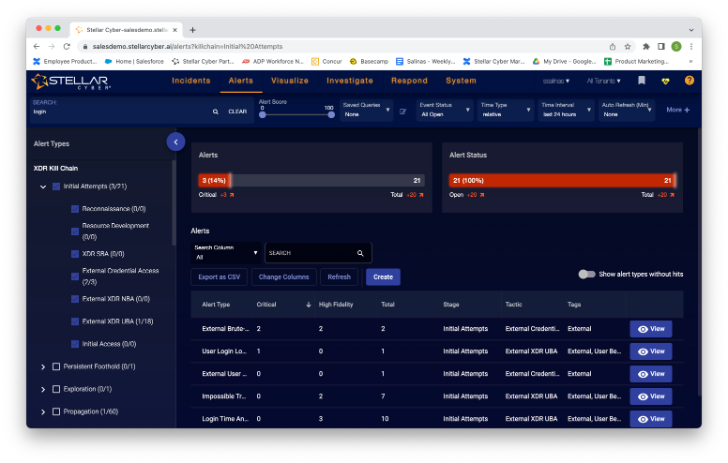
Here I can see these alerts with the stage “Initial Attempts”
set by Stellar Cyber automatically. Further down the rabbit hole, I
see more information about the alert when I click “View” on any of
the alerts. Initially, I was presented with some summary graphs,
then scrolling down the screen a bit, I saw a “more info”
hyperlink, so I clicked it and got this in return.
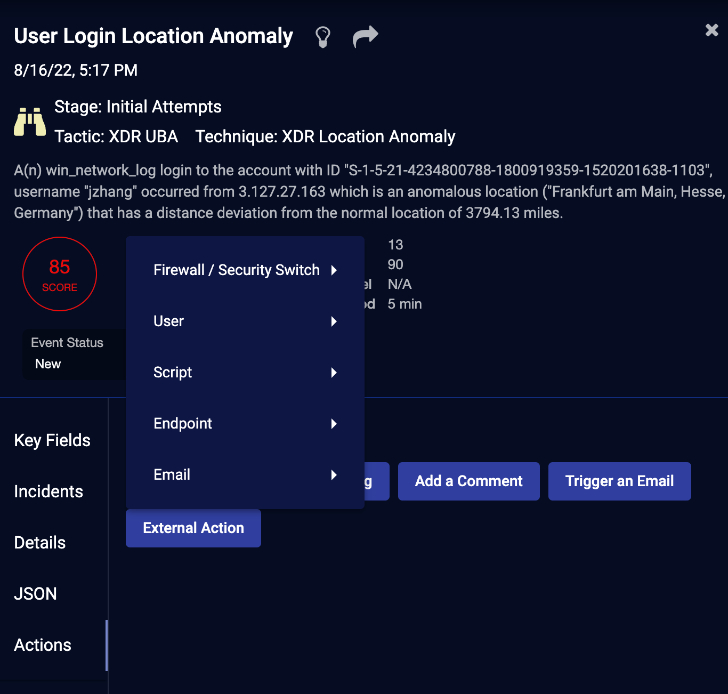
Here I can read about the incident, dig into the details, and
review the raw data behind this incident as well as the JSON, which
I can conveniently copy to a clipboard if necessary.
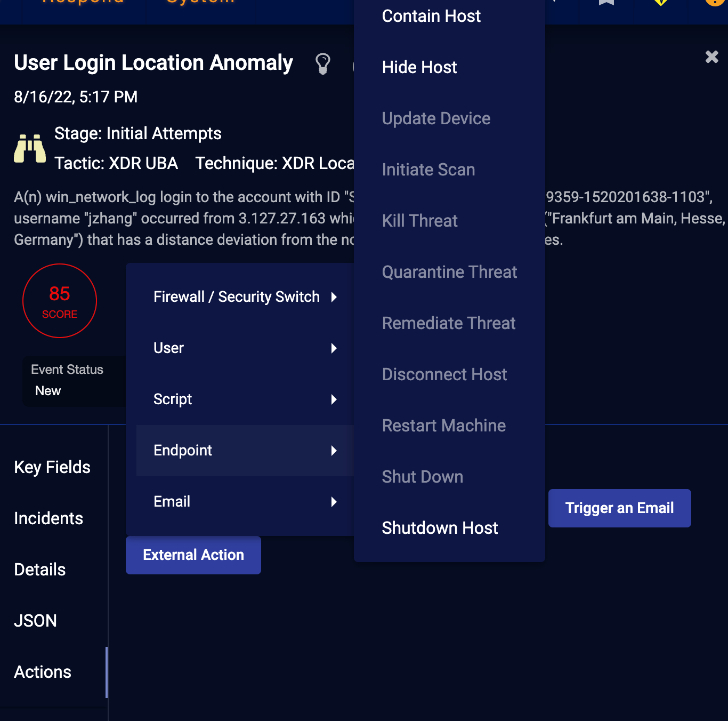
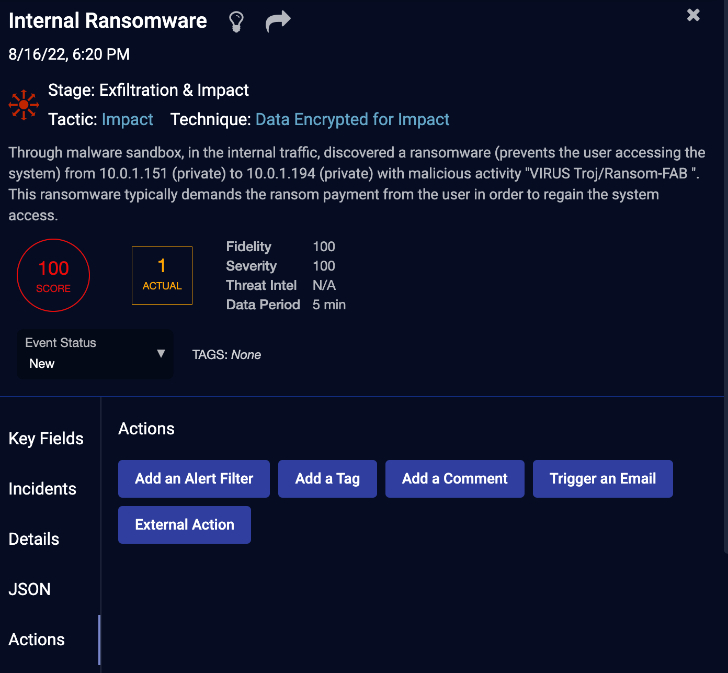
Here is where I thought things got a bit more interesting. While
the presentation of the data in Stellar Cyber is easy to understand
and logical, the product’s true power was not evident to me until I
clicked on the “Actions” button on the screen above.
As you can see, I can take my response actions right from this
screen, such as “add a filter, trigger an email, or take external
action. Clicking on external action, I get another picklist. When I
click on Endpoint, I get a long list of options from contain host
to shutdown host.
When clicking on an action, like contain host, a configuration
dialog displays where I can select the connector to use, the target
of the action, and any other options required to initiate the
action chosen. So, in summary, I can see how security analysts,
especially junior ones, will find this workflow very useful in that
they can a) easily dig into the details of an incident from the
home screen, b) review even more details by going deeper into the
data, and c) take a remediation action from this screen without
writing any scripts or tinkering with a code.
For MSSPs, I could see onboarding new analysts to work on this
view initially to familiarize them with the platform while still
helping meet customer service level agreements. However, my gut
tells me that there is much more to learn about this Stellar Cyber
platform so let’s see if there is another path to investigating
incidents.
Exploring Incidents
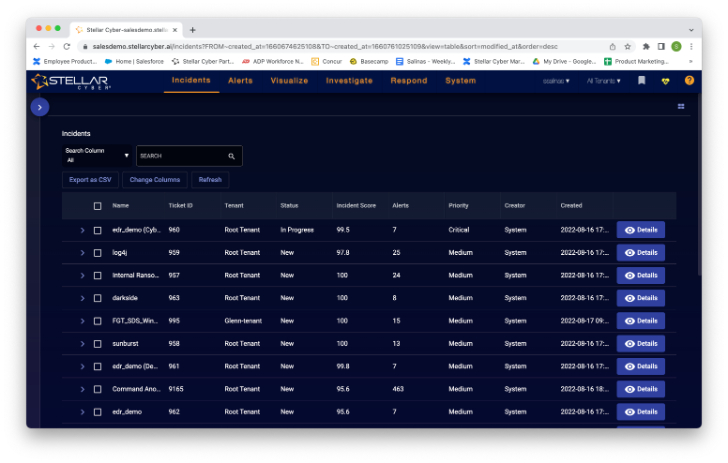
Now instead of clicking on the Open XDR Kill Chain, I am going
to click on the menu item “Incidents” and get this screen in
return.
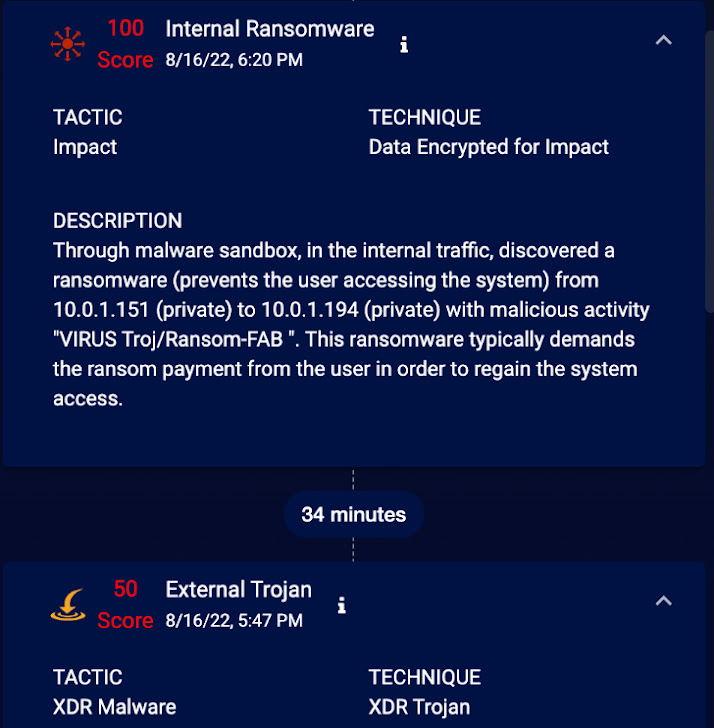
When I clicked on the carrot in the blue circle, it expanded a
filtering list that enabled me to hone in on a specific type of
incident. Since I am in exploratory mode, I go directly to the
details button to see what I can find in this detail view.
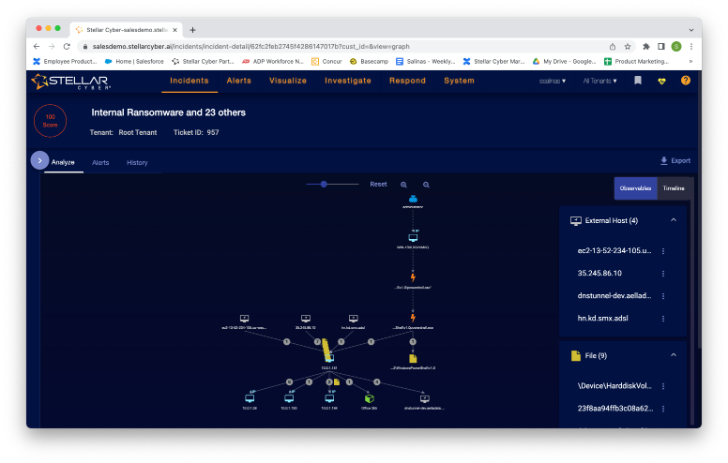
Now I can see how this incident occurred and propagated across
multiple assets. Further, I can automatically see the files,
processes, users, and services associated with the incident. There
are different ways to view this data as well. For example, I could
switch to the timeline view to get a readable history of this
incident, like below:
When I click on the small “i,” I get to a familiar screen.
I know the story from here, which is good.
So, in summary, I can see that analysts who are used to working
from a list of alerts may like to start their investigations from
the incidents page. For MSSPs, this view is also beneficial as it
shows all incidents across all tenants in a single view. Of course,
you can limit this view by analysts, customers, etc.
Threat Hunting and Response Actions in Stellar
Cyber
By this time, I am convinced Stellar Cyber offers an interesting
approach for MSSPs looking to streamline their security operations.
Frankly, at this point in my review, I haven’t had to write any
special scripts or do anything other than clicking some links and
scrolling around some screens to hypothetically respond to some
nasty alerts, which is not the norm for these types of
products.
Before singing the praises of Stellar Cyber too highly, I wanted
to take a look at a couple of other stated features, Threat Hunting
and response actions (aka SOAR). Let’s start with threat hunting.
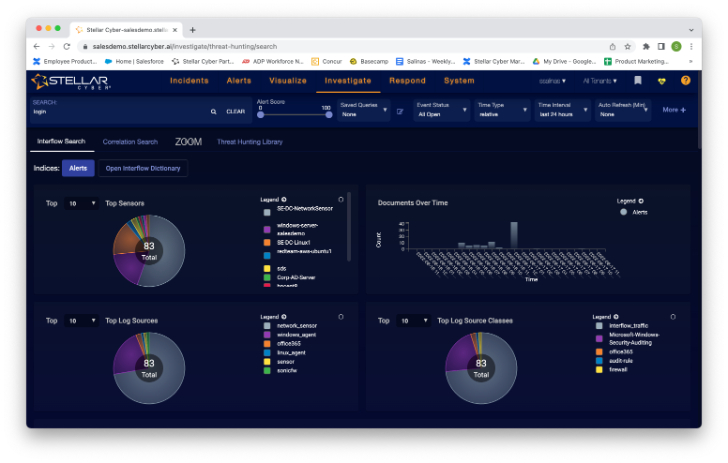
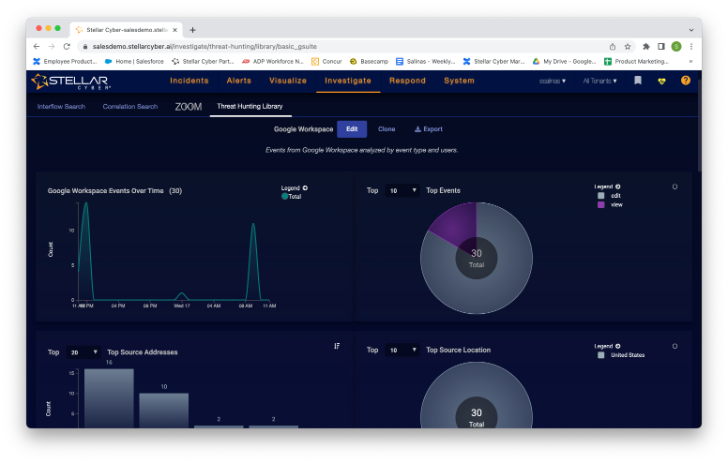
When I click on “Threat Hunting” from the menu, I am presented with
this screen.
While these stats are interesting, I am looking for actionable
threat h; that’s where I see the search dialog box on the top
right. I type in login and notice the stats change dynamically.
Scrolling down the screen, I also see a list of alerts that has
been filtered base on my search term. Here I see the familiar “more
info” option, so I know where that will take me.
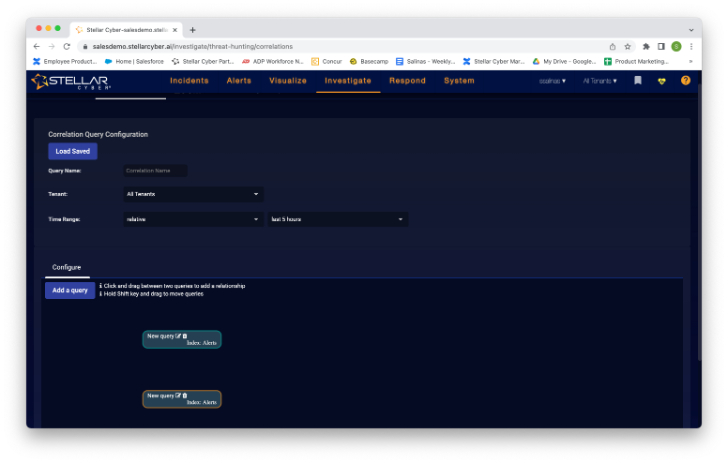
I also noticed something called “correlation search” under the
search dialog box. When I click that, my screen changes to
this.
I can load a saved query or add a new query. Clicking the add
query, I see this query builder. This enables me to search
essentially any data Stellar Cyber stores to theoretically find
threats that went unnoticed. I can also access the threat hunting
library to access previously saved queries.
You can also create response actions that will run automatically
if the query you create returns any matches.
So, in summary, Stellar Cyber offers a simple threat hunting
platform that doesn’t require you to build your own ELK stack or be
a power scripter. For MSSPs, I can see this being a nice value add
they can offer customers when emerging threats are discovered in
the wild.
Conclusion
Stellar Cyber is a solid security operations platform with many
features for the MSSP user. If you are in the market for a new
SecOps platform, it is worth taking a look[2]
at what Stellar Cyber has to offer.
References
- ^
Stellar
Cyber (stellarcyber.com) - ^
taking a
look (stellarcyber.ai)
Read more https://thehackernews.com/2022/08/hands-on-review-stellar-cyber-security.html