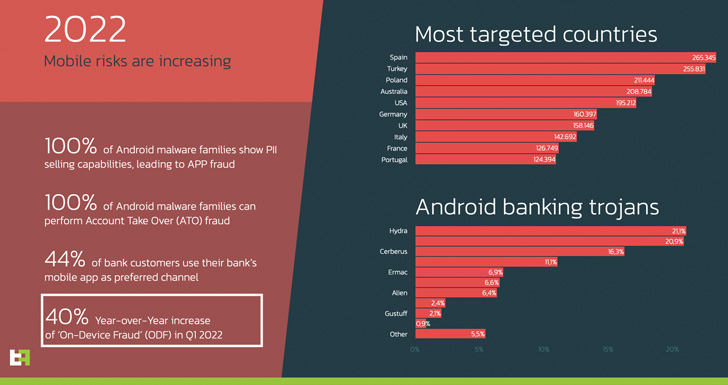
An analysis of the mobile threat landscape in 2022 shows that
Spain and Turkey are the most targeted countries for malware
campaigns, even as a mix of new and existing banking trojans are
increasingly targeting Android devices to conduct on-device fraud
(ODF).
Other frequently targeted countries include Poland, Australia,
the U.S., Germany, the U.K., Italy, France, and Portugal.
“The most worrying leitmotif is the increasing attention to
On-Device Fraud (ODF),” Dutch cybersecurity company ThreatFabric
said[1]
in a report shared with The Hacker News.
“Just in the first five months of 2022 there has been an
increase of more than 40% in malware families that abuse Android OS
to perform fraud using the device itself, making it almost
impossible to detect them using traditional fraud scoring
engines.”
Hydra[2], FluBot[3]
(aka Cabassous), Cerberus[4], Octo[5], and ERMAC[6]
accounted for the most active banking trojans based on the number
of samples observed during the same period.
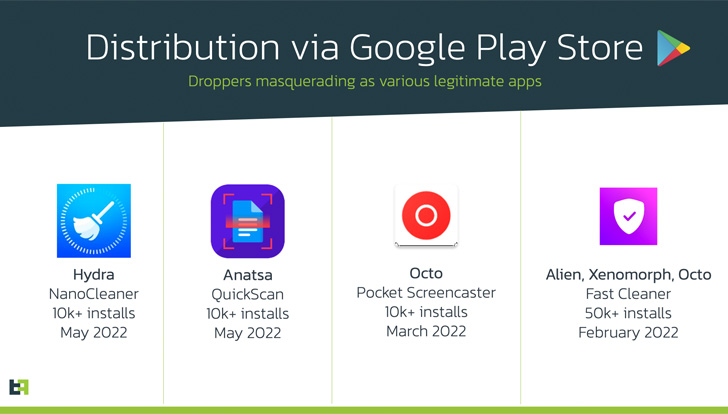
Accompanying this trend is the continued discovery of new
dropper apps on Google Play Store that come under the guise of
seemingly innocuous productivity and utility applications to
distribute the malware –
- Nano Cleaner (com.casualplay.leadbro)
- QuickScan (com.zynksoftware.docuscanapp)
- Chrome (com.talkleadihr)
- Play Store (com.girltold85)
- Pocket Screencaster (com.cutthousandjs)
- Chrome (com.biyitunixiko.populolo)
- Chrome (Mobile com.xifoforezuma.kebo)
- BAWAG PSK Security (com.qjlpfydjb.bpycogkzm)
What’s more, on-device fraud — which refers to a stealthy method
of initiating rogue transactions from victim’s devices — has made
it feasible to use previously stolen credentials to login to
banking applications and carry out financial transactions.
To make matters worse, the banking trojans have also been
observed constantly updating their capabilities, with Octo devising
an improved method to steal credentials from overlay screens even
before they are submitted.
“This is done in order to be able to get the credentials even if
[the] victim suspected something and closed the overlay without
actually pressing the fake ‘login’ present in the overlay page,”
the researchers explained.
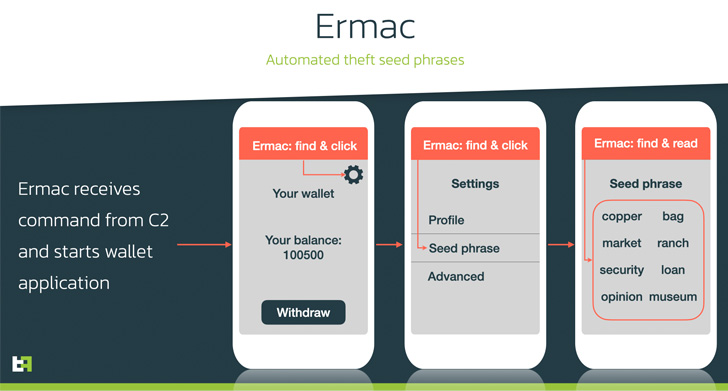
ERMAC, which emerged last September, has received noticeable
upgrades of its own that allow it to siphon seed phrases from
different cryptocurrency wallet apps in an automated fashion by
taking advantage of Android’s Accessibility Service[7].
Accessibility Service has been Android’s Achilles’ heel in
recent years, allowing threat actors to leverage[8]
the legitimate API[9]
to serve unsuspecting users with fake overlay screens and capture
sensitive information.
Last year, Google attempted[10] to tackle the problem
by ensuring that “only services that are designed to help people
with disabilities access their device or otherwise overcome
challenges stemming from their disabilities are eligible to declare
that they are accessibility tools.”
But the tech giant is going a step further in Android 13, which
is currently in beta, by restricting API access for apps that the
user has sideloaded from outside of an app store, effectively
making it harder for potentially harmful apps to misuse the
service.
That said, ThreatFabric noted it was able to bypass these
restrictions trivially by means of a tweaked installation process,
suggesting the need for a more stricter approach to counteract such
threats.
It’s recommended that users stick to downloading apps from the
Google Play Store, avoid granting unusual permissions to apps that
have no purpose asking for them (e.g., a calculator app asking to
access contact lists), and watch out for any phishing attempts
aimed at installing rogue apps.
“The openness of Android OS serves both good and bad as malware
continues to abuse the legitimate features, whilst upcoming
restrictions seem to hardly interfere with the malicious intentions
of such apps,” the researchers said.
References
- ^
said
(threatfabric.com) - ^
Hydra
(thehackernews.com) - ^
FluBot
(thehackernews.com) - ^
Cerberus
(thehackernews.com) - ^
Octo
(thehackernews.com) - ^
ERMAC
(thehackernews.com) - ^
Accessibility Service
(developer.android.com) - ^
leverage
(thehackernews.com) - ^
legitimate API
(thehackernews.com) - ^
attempted
(support.google.com)
Read more https://thehackernews.com/2022/05/latest-mobile-malware-report-suggests.html