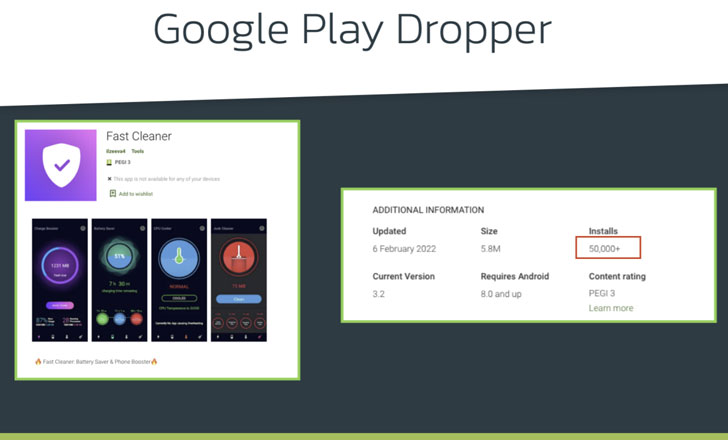
A new Android banking trojan with over 50,000 installations has
been observed distributed via the official Google Play Store with
the goal of targeting 56 European banks and carrying out harvesting
sensitive information from compromised devices.
Dubbed Xenomorph[1]
by Dutch security firm ThreatFabric, the in-development malware is
said to share overlaps with another banking trojan tracked under
the moniker Alien while also being “radically different” from its
predecessor in terms of the functionalities offered.
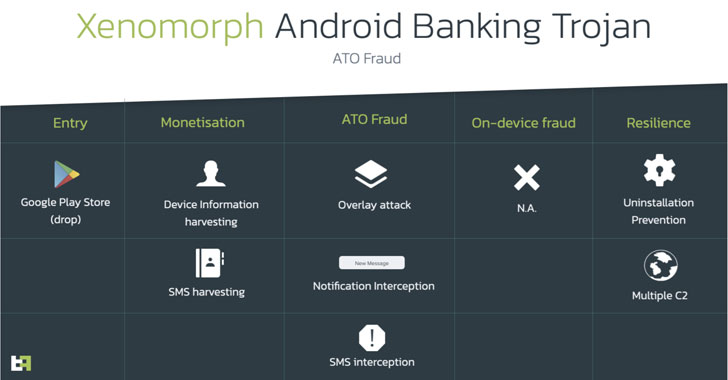
“Despite being a work-in-progress, Xenomorph is already sporting
effective overlays and being actively distributed on official app
stores,” ThreatFabric’s founder and CEO, Han Sahin, said. “In
addition, it features a very detailed and modular engine to abuse
accessibility services, which in the future could power very
advanced capabilities, like ATS.”
Alien, a remote access trojan (RAT) with notification sniffing
and authenticator-based 2FA theft features, emerged shortly[2]
after the demise of the infamous Cerberus[3]
malware in August 2020. Since then, other forks of Cerberus have
been spotted in the wild, including ERMAC[4]
in September 2021.
Xenomorph, like Alien and ERMAC, is yet another example of an
Android banking trojan that’s focused on circumventing Google Play
Store’s security protections by masquerading as productivity apps
such as “Fast Cleaner” to trick unaware victims into installing the
malware.
It’s worth noting that a fitness training dropper app with over
10,000 installations — dubbed GymDrop[5]
— was found delivering the Alien banking trojan payload in November
by masking it as a “new package of workout exercises.”
Fast Cleaner, which has the package name “vizeeva.fast.cleaner”
and continues to available on the app store, has been most popular
in Portugal and Spain, data from mobile app market intelligence
firm Sensor Tower reveals[6], with the app making its
first appearance in the Play Store towards the end of January
2022.
What’s more, reviews for the app from users warned that “this
app has malware” and that it “ask[s] for an update to be confirmed
continuously.” Another user said: “It puts malware on the device
and apart from that it has a self-protection system so that you
cannot uninstall it.”
Also put to use by Xenomorph is the time-tested tactic[7]
of prompting the victims to grant it Accessibility Service
privileges and abuse the permissions to conduct overlay attacks,
wherein the malware injects rogue overlay screens atop targeted
apps from Spain, Portugal, Italy, and Belgium to siphon credentials
and other personal information.
Additionally, it’s equipped with a notification interception
feature to extract two-factor authentication tokens received via
SMS, and get the list of installed apps, the results of which are
exfiltrated to a remote command-and-control server.
“The surfacing of Xenomorph shows, once again, that threat
actors are focusing their attention on landing applications on
official markets,” the researchers said. “Modern Banking malware is
evolving at a very fast rate, and criminals are starting to adopt
more refined development practices to support future updates.”
References
Read more https://thehackernews.com/2022/02/xenomorph-android-banking.html