Cybersecurity researchers today uncovered a new
Cybersecurity researchers today uncovered a newstrain of banking malware that targets not only banking apps but
also steals data and credentials from social networking, dating,
and cryptocurrency apps—in total 337 non-financial Android
applications on it’s target list.
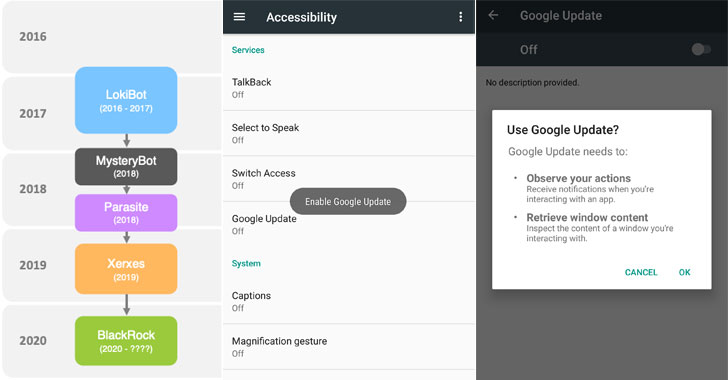
Dubbed “BlackRock[1]” by ThreatFabric
researchers, which discovered the trojan in May, its source code is
derived from a leaked version of Xerxes banking malware, which
itself is a strain of the LokiBot Android
banking trojan[2]
that was first observed during 2016-2017.
Chief among its features are stealing user credentials,
intercepting SMS messages, hijacking notifications, and even
recording keystrokes from the targeted apps, in addition to being
capable of hiding from antivirus software.
“Not only did the [BlackRock] Trojan undergo changes in its code,
but also comes with an increased target list and has been ongoing
for a longer period,” ThreatFabric said.
“It contains an important number of social, networking,
communication and dating applications [that] haven’t been observed
in target lists for other existing banking Trojans.”
BlackRock does the data collection by abusing Android’s
Accessibility Service privileges, for which it seeks users’
permissions under the guise of fake Google updates when it’s
launched for the first time on the device, as shown in the shared
screenshots.
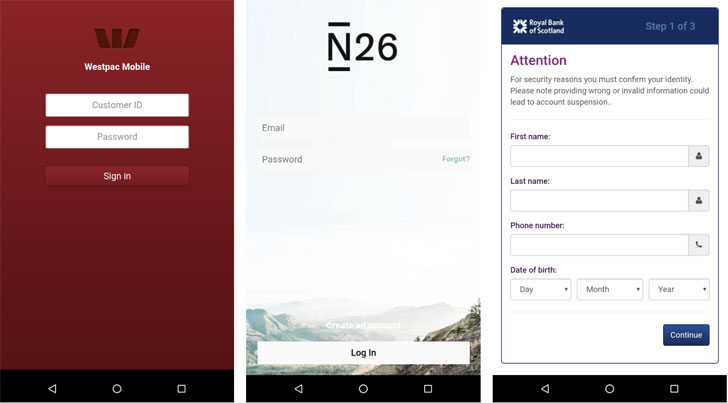
Subsequently, it goes on to grant itself additional permissions
and establish a connection with a remote command-and-control (C2)
server to carry out its malicious activities by injecting overlays
atop the login and payment screens of the targeted apps.
These credential-stealing overlays have been found on banking
apps operating in Europe, Australia, the US, and Canada, as well as
shopping, communication, and business apps.
“The target list of non-financial apps contains famous applications
such as but not limited to Tinder, TikTok, PlayStation, Facebook,
Instagram, Skype, Snapchat, Twitter, Grinder, VK, Netflix, Uber,
eBay, Amazon, Reddit and Tumblr,” the researchers told The Hacker
News.
This is not the first time mobile malware has abused Android’s
accessibility features.
Earlier this year, IBM X-Force researchers detailed a new TrickBot
campaign, called TrickMo, that
was found exclusively targeting German users with malware that
misused accessibility features to intercept one-time passwords
(OTP), mobile TAN (mTAN), and pushTAN authentication codes.
Then in April, Cybereason uncovered a different class of banking
malware known as EventBot[4] that leveraged the same
feature to exfiltrate sensitive data from financial applications,
read user SMS messages, and hijack SMS-based two-factor
authentication codes.
What makes BlackRock’s campaign different is the sheer breadth
of the apps targeted, which go beyond the mobile banking apps that
are usually targeted.
“After Alien, Eventbot, and BlackRock we can expect that
financially motivated threat actors will build new banking Trojans
and continue improving the existing ones,” ThreatFabric researchers
concluded.
“With the changes that we expect to be made to mobile banking
Trojans, the line between banking malware and spyware becomes
thinner, [and] banking malware will pose a threat for more
organizations.”
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/qGGAlqCWJ6E/android-password-hacker.html