Cybersecurity researchers have disclosed a new ransomware strain
called GoodWill that compels victims into donating
for social causes and provide financial assistance to people in
need.
“The ransomware group propagates very unusual demands in
exchange for the decryption key,” researchers from CloudSEK
said[1]
in a report published last week. “The Robin Hood-like group claims
to be interested in helping the less fortunate, rather than
extorting victims for financial motivations.”
Written in .NET, the ransomware was first identified by the
India-based cybersecurity firm in March 2022, with the infections
rendering sensitive files inaccessible without decrypting them. The
malware, which makes use of the AES algorithm[2]
for encryption, is also notable for sleeping for 722.45 seconds to
interfere with dynamic analysis.
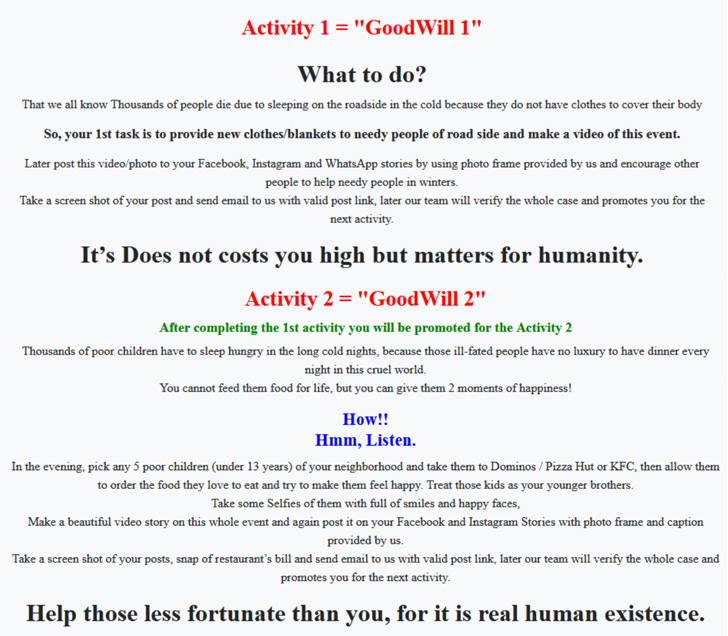
The encryption process is followed by displaying a
multiple-paged ransom note that requires the victims to carry out
three socially-driven activities to be able to obtain the
decryption kit.
This includes donating new clothes and blankets to the homeless,
taking any five underprivileged children to Domino’s Pizza, Pizza
Hut, or KFC for a treat, and offering financial support to patients
who need urgent medical attention but don’t have the financial
means to do so.
Additionally, the victims are asked to record the activities in
the form of screenshots and selfies and post them as evidence on
their social media accounts.
“Once all three activities are completed, the victims should
also write a note on social media (Facebook or Instagram) on ‘How
you transformed yourself into a kind human being by becoming a
victim of a ransomware called GoodWill,'” the researchers said.
There are no known victims of GoodWill and their exact tactics,
techniques, and procedures (TTPs) used to facilitate the attacks
are unclear as yet.
Also unrecognized is the identity of the threat actor, although
an analysis of the email address and network artifacts suggests
that the operators are from India and that they speak Hindi.
Further investigation into the ransomware sample has also
revealed significant overlaps with another Windows-based strain
called HiddenTear[3], the first ransomware to
have been open-sourced as a proof-of-concept (PoC) back in 2015 by
a Turkish programmer.
“GoodWill operators may have gained access to this allowing them
to create a new ransomware with necessary modifications,” the
researchers said.
References
- ^
said
(cloudsek.com) - ^
AES
algorithm (en.wikipedia.org) - ^
HiddenTear
(malpedia.caad.fkie.fraunhofer.de)
Read more https://thehackernews.com/2022/05/new-goodwill-ransomware-forces-victims.html