A new IoT botnet malware dubbed RapperBot has been
observed rapidly evolving its capabilities since it was first
discovered in mid-June 2022.
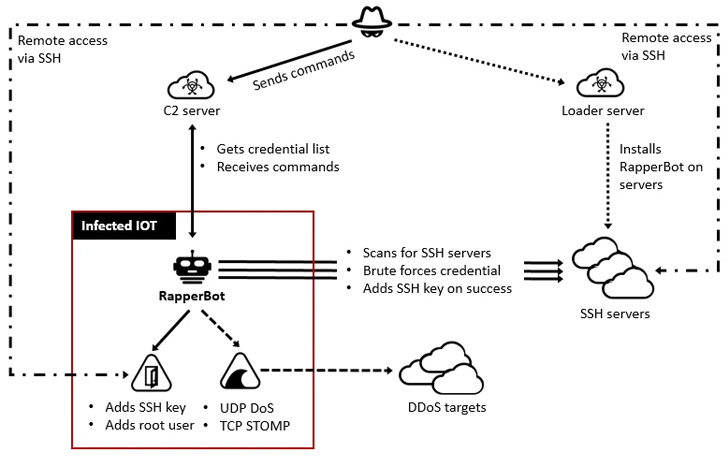
“This family borrows heavily from the original Mirai source code[1], but what separates it
from other IoT malware families is its built-in capability to brute
force credentials and gain access to SSH servers instead of Telnet
as implemented in Mirai,” Fortinet FortiGuard Labs said[2]
in a report.
The malware, which gets its name from an embedded URL to a
YouTube rap music video in an earlier version, is said to have
amassed a growing collection of compromised SSH servers, with over
3,500 unique IP addresses used to scan and brute-force their way
into the servers.
RapperBot’s current implementation also delineates it from
Mirai, allowing it to primarily function as an SSH brute-force tool
with limited capabilities to carry out distributed
denial-of-service (DDoS) attacks.
The deviation from traditional Mirai behavior is further
evidenced in its attempt to establish persistence on the
compromised host, effectively permitting the threat actor to
maintain long-term access long after the malware has been removed
or the device has been rebooted.
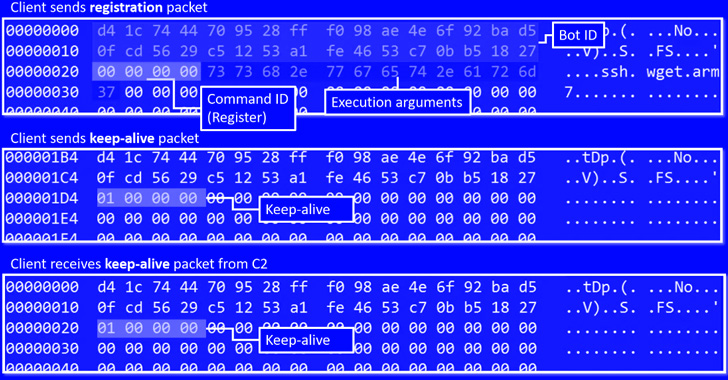
The attacks entail brute-forcing potential targets using a list
of credentials received from a remote server. Upon successfully
breaking into a vulnerable SSH server, the valid credentials are
exfiltrated back to the command-and-control.
“Since mid-July, RapperBot has switched from self-propagation to
maintaining remote access into the brute-forced SSH servers,” the
researchers said.
The access is achieved by adding the operators’ SSH public key
to a special file called “~/.ssh/authorized_keys[3],” permitting the
adversary to connect and authenticate to the server using the
corresponding private private key without having to furnish a
password.
“This presents a threat to compromised SSH servers as threat
actors can access them even after SSH credentials have been changed
or SSH password authentication is disabled,” the researchers
explained.
“Moreover, since the file is replaced, all existing authorized
keys are deleted, which prevents legitimate users from accessing
the SSH server via public key authentication.”
The shift also enables the malware to maintain its access to
these hacked devices via SSH, permitting the actor to leverage the
foothold to conduct Mirai-styled denial-of-service attacks.
These differences from other IoT malware families have had the
side-effect of making its primary motivations something of a
mystery, a fact further complicated by the fact that RapperBot’s
authors have left little-to-no telltale signs of their
provenance.
The ditching of self-propagation in favor of persistence
notwithstanding, the botnet is said to have undergone significant
changes in a short span of time, chief among them being the removal
of DDoS attack features from the artifacts at one point, only to be
reintroduced a week later.
The objectives of the campaign, ultimately, remain nebulous at
best, with no follow-on activity observed post a successful
compromise. What’s clear is that SSH servers with default or
guessable credentials are being corralled into a botnet for some
unspecified future purpose.
To fend off such infections, it’s recommended that users set
strong passwords for devices or disable password authentication for
SSH where possible.
“Although this threat heavily borrows code from Mirai, it has
features that set it apart from its predecessor and its variants,”
the researchers said. “Its ability to persist in the victim system
gives threat actors the flexibility to use them for any malicious
purpose they desire.”
References
- ^
Mirai
source code (thehackernews.com) - ^
said
(www.fortinet.com) - ^
~/.ssh/authorized_keys
(www.digitalocean.com)
Read more https://thehackernews.com/2022/08/new-iot-rapperbot-malware-targeting.html