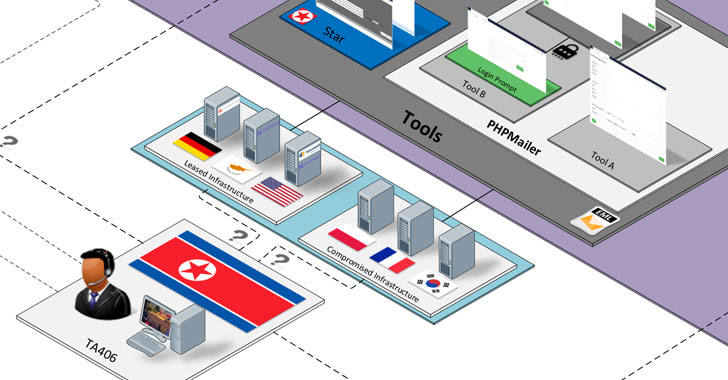
A threat actor with ties to North Korea has been linked to a
prolific wave of credential theft campaigns targeting research,
education, government, media and other organizations, with two of
the attacks also attempting to distribute malware that could be
used for intelligence gathering.
Enterprise security firm Proofpoint attributed[1]
the infiltrations to a group it tracks as TA406[2], and by the wider threat
intelligence community under the monikers Kimsuky[3]
(Kaspersky[4]), Velvet Chollima
(CrowdStrike[5]), Thallium (Microsoft[6]), Black Banshee
(PwC[7]), ITG16 (IBM[8]), and the Konni Group
(Cisco Talos[9]).
Policy experts, journalists and nongovernmental organizations
(NGOs) were targeted as part of weekly campaigns observed between
from January through June 2021, Proofpoint researchers Darien Huss
and Selena Larson disclosed in a technical report detailing the
actor’s tactics, techniques, and procedures (TTPs), with the
attacks spread across North America, Russia, China, and South
Korea.
Known to be operational as early as 2012, Kimsuky has since
emerged as one of the most active advanced persistent threat (APT)
group known for setting its sights on cyber espionage but also for
conducting attacks for financial gain, targeting government
entities, think tanks, and individuals identified as experts in
various fields as well as harvest sensitive information pertaining
to foreign policy and national security issues.
“Like other APT groups that constitute a big umbrella, Kimsuky
contains several clusters: BabyShark[10], AppleSeed[11], Flower Power, and Gold
Dragon,” Kaspersky researchers noted[12] in their Q2 2021 APT
trends report published last month. The AppleSeed sub-group is also
referred to as TA408.
The group is also known for reeling in targets with convincing
social engineering schemes and watering hole attacks before sending
them malware-infected payloads or tricking them into submitting
sensitive credentials to phishing sites, the U.S. Cybersecurity and
Infrastructure Security Agency (CISA) said[13] in a public alert
issued in October 2020.
Earlier this month, researchers from Cisco Talos disclosed an
ongoing Kimsuky campaign since June 2021 that was found leveraging
malicious blogs hosted on Google’s Blogger platform to target
high-value South Korean targets, including geopolitical and
aerospace research agencies, with the goal of delivering a
“constantly evolving set of implants derived from the Gold
Dragon/Brave Prince family” that act as file exfiltrators,
information gatherers, and credential stealers for reconnaissance,
espionage, and credential harvesting.
“This campaign begins with malicious Microsoft Office documents
(maldocs) containing macros being delivered to victims,” Talos
researchers explained[14]. “The infection chain
results in the malware reaching out to malicious blogs set up by
the attackers. These blogs provide the attackers the ability to
update the malicious content posted in the blog depending on
whether a victim is of value to the attackers.”
Now in what appears to be a further ramping up of attacks, the
threat actor simultaneously commenced near-weekly email threat
campaigns using the identities of legitimate policy experts, while
featuring themes related to nuclear weapon safety, politics, and
Korean foreign policy, ultimately luring the targeted individuals
to give up their corporate credentials via a rogue URL embedded in
the messages that redirect the victims to custom
credential-harvesting pages.
Kimsuky’s phishing campaigns had a noticeable shift in March
2021 when the emails moved beyond credential theft to become a
medium for distributing malware, coinciding with North Korea’s
missile tests[15] conducted later that
month.
The emails included a link that sent the target to an
attacker-controlled domain used to trick targets into downloading a
compressed archive incorporating a binary, which is orchestrated to
create a scheduled task that is executed every 15 minutes to
install additional malware from a remote server. However, the
ultimate motive behind the attacks remains unclear as no follow-on
payloads were observed.
Another notable attack in June resulted in the deployment of a
downloader (“FatBoy”) using an HTML attachment lure that was then
used to retrieve a next-stage reconnaissance script capable of
collecting “extensive information” about the targeted device.
Proofpoint said that both the campaigns exhibited overlaps with
attacks previously[16] identified[17] as mounted by the Konni
Group.
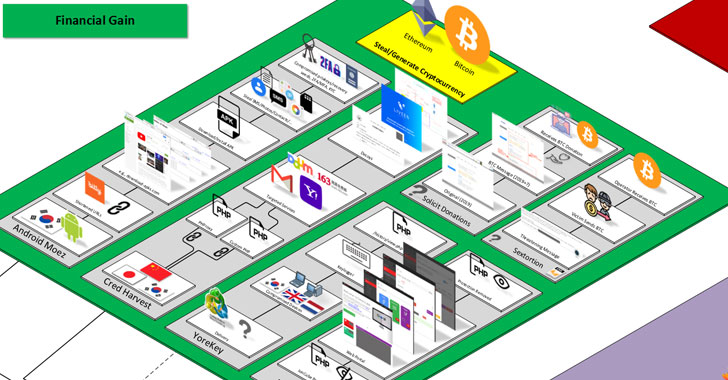
Other notable tools in its malware arsenal encompass a Windows
keylogger dubbed YoreKey, a number of rogue Android apps striking
cryptocurrency users in South Korea, a deobfuscation service named
Deioncube to decode files encrypted with ionCube[18]‘s source code
protection software, and a sextortion scam that urges email
recipients to transfer an amount worth $500 in bitcoin to a valid
wallet associated with a South Korea-based NGO.
“It’s unknown whether the NGO was compromised, and the donation
message was placed on their website maliciously, or if there’s
another explanation,” the researchers said. “As of June 2021, the
associated bitcoin wallet had received and sent about 3.77
bitcoin.”
References
- ^
attributed
(www.proofpoint.com) - ^
TA406
(attack.mitre.org) - ^
Kimsuky
(malpedia.caad.fkie.fraunhofer.de) - ^
Kaspersky
(securelist.com) - ^
CrowdStrike
(www.crowdstrike.com) - ^
Microsoft
(blogs.microsoft.com) - ^
PwC
(www.pwc.co.uk) - ^
IBM
(securityintelligence.com) - ^
Cisco
Talos (blog.talosintelligence.com) - ^
BabyShark
(thehackernews.com) - ^
AppleSeed
(thehackernews.com) - ^
noted
(securelist.com) - ^
said
(us-cert.cisa.gov) - ^
explained
(blog.talosintelligence.com) - ^
missile tests
(en.wikipedia.org) - ^
previously
(unit42.paloaltonetworks.com) - ^
identified
(blog.malwarebytes.com) - ^
ionCube
(en.wikipedia.org)
Read more https://thehackernews.com/2021/11/north-korean-hackers-found-behind-range.html