A Russian-speaking ransomware group dubbed OldGremlin has
been attributed to 16 malicious campaigns aimed at entities
operating in the transcontinental Eurasian nation over the course
of two and a half years.
“The group’s victims include companies in sectors such as
logistics, industry, insurance, retail, real estate, software
development, and banking,” Group-IB said[1]
in an exhaustive report shared with The Hacker News. “In 2020, the
group even targeted an arms manufacturer.”
In what’s a rarity in the ransomware landscape, OldGremlin (aka
TinyScouts) is one of the very few financially motivated cybercrime
gangs that primarily focuses on Russian companies.
Other notable groups consist of Dharma, Crylock, and Thanos,
contributing to an uptick in ransomware attacks targeting
businesses in the country by over 200% in 2021.
OldGremlin first came to light in September 2020 when the
Singapore-headquartered cybersecurity company disclosed[2]
nine campaigns orchestrated by the actor between May and August.
The first attack was detected in early April 2020.
In all, the group is said to have conducted 10 phishing email
campaigns in 2020, followed by one highly successful attack in 2021
and five more in 2022, with ransom demands touching a record $16.9
million.
“OldGremlin thoroughly studies their victims,” Group-IB
explained. “The demanded ransom is therefore often proportional to
the company’s size and revenue and is obviously higher than the
budget necessary for ensuring a suitable level of information
security.”
Known to mainly target enterprise networks running on Windows,
attacks mounted by OldGremlin have leveraged phishing emails
masquerading as tax and legal services companies to dupe victims
into clicking on fraudulent links and downloading malicious files,
allowing the attackers to worm their way inside the networks.
“The threat actors often pose as well-known companies, including
the media group RBC, the legal assistance system Consultant Plus,
the company 1C-Bitrix, the Russian Union of Industrialists and
Entrepreneurs, and Minsk Tractor Works,” Group-IB said.
Upon gaining an initial foothold, OldGremlin moves to establish
persistence by creating scheduled tasks, gaining elevated
privileges using Cobalt Stroke, and even flaw in Cisco AnyConnect
(CVE-2020-3153[3]
and CVE-2020-3433[4]), while also gaining
remote access to the compromised infrastructure using tools such as
TeamViewer.
Some of the aspects that make the crew stand out from other
ransomware groups is that it doesn’t rely on double extortion to
coerce targeted companies into paying up despite exfiltrating the
data. It has also been observed taking long breaks after each
successful attack.
What’s more, the average dwell time until ransomware deployment
has been pegged at 49 days, well above the reported 11 day median dwell time[5], suggesting extended
efforts on part of the actor to examine the breached domain (which
is achieved using a tool called TinyScout).
OldGremlin’s most recent phishing wave occurred on August 23,
2022, with emails embedding links pointing to a ZIP archive payload
hosted on Dropbox to activate the killchain.
These archive files, in turn, harbor a rogue LNK file (dubbed
TinyLink) that downloads a backdoor called TinyFluff, which is one
among the four implants used by the group: TinyPosh, TinyNode, and
TinyShell, before deleting data backups and dropping the .NET-based
TinyCrypt ransomware.
- TinyPosh: A PowerShell trojan engineered to collect and
transfer sensitive information about the infected system to a
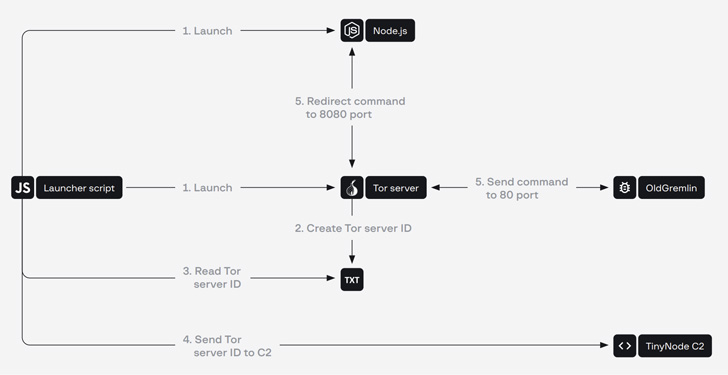
remote server, and launch additional PowerShell scripts. - TinyNode: A backdoor that runs the Node.js interpreter to
execute commands received from a command-and-control (C2) server
over the Tor network. - TinyFluff: A successor[6]
to TinyNode, which is used as the primary downloader for receiving
and running malicious scripts.
Also put to use by OldGremlin are other tools such as TinyShot,
a console utility for capturing screenshots, TinyKiller, which
kills antivirus processes via a bring your own vulnerable driver
(BYOVD) attack targeting gdrv.sys and RTCore64.sys drivers.
It’s worth noting that the operators behind the BlackByte
ransomware group were also recently found leveraging the same flaw[7] in the RTCore64.sys
driver to turn off security solutions in the hacked machines.
One other unusual application used by OldGremlin in its attacks
is a .NET console app called TinyIsolator, which temporarily cuts
off the host from the network by disabling network adaptors prior
to executing the ransomware.
On top of that, the group’s malware arsenal encompasses a Linux
version of TinyCrypt, which is written in GO and launched after
deleting .bash_history files, changing user passwords to limit
access to the compromised host, and disabling SSH.
“OldGremlin has debunked the myth that ransomware groups are
indifferent to Russian companies,” Ivan Pisarev, head of dynamic
malware analysis team at Group-IB, said.
“Despite the fact that OldGremlin has been focusing on Russia so
far, they should not be underestimated elsewhere. Many
Russian-speaking gangs started off by targeting companies in
post-Soviet space and then switched to other geographies.”
References
- ^
said
(www.group-ib.com) - ^
disclosed
(thehackernews.com) - ^
CVE-2020-3153
(nvd.nist.gov) - ^
CVE-2020-3433
(nvd.nist.gov) - ^
11 day
median dwell time (www.sophos.com) - ^
successor
(blog.group-ib.com) - ^
leveraging the same flaw
(thehackernews.com)
Read more https://thehackernews.com/2022/10/oldgremlin-ransomware-targeted-over.html