Cybersecurity researchers have demonstrated a new attack
technique that makes it possible to leverage a device’s Bluetooth
component to directly extract network passwords and manipulate
traffic on a Wi-Fi chip.
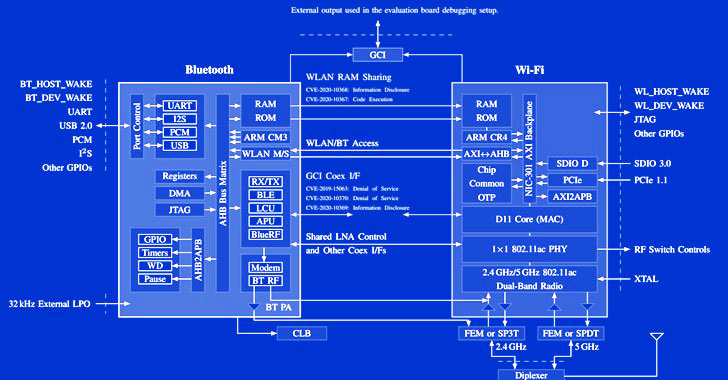
The novel attacks work against the so-called “combo chips,”
which are specialized chips that are equipped to handle different
types of radio wave-based wireless communications, such as Wi-Fi,
Bluetooth, and LTE.
“We provide empirical evidence that coexistence, i.e., the
coordination of cross-technology wireless transmissions, is an
unexplored attack surface,” a group of researchers from the
Technical University of Darmstadt’s Secure Mobile Networking Lab
and the University of Brescia said in a new
paper[1].
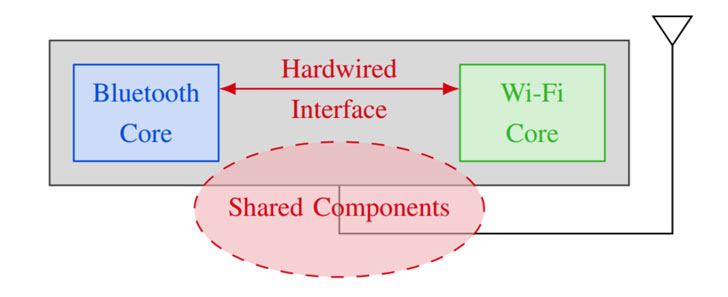
“Instead of escalating directly into the mobile [operating
system], wireless chips can escalate their privileges into other
wireless chips by exploiting the same mechanisms they use to
arbitrate their access to the resources they share, i.e., the
transmitting antenna and the wireless medium.”
Coexistence[2]
refers to a mechanism wherein Bluetooth, Wi-Fi, and LTE share the
same components and resources — e.g., antenna or wireless spectrum
— necessitating that these communication standards coordinate the
spectrum access to avoid collisions when operating in the same
frequency. Chipset vendors use this principle to allow Wi-Fi and
Bluetooth to operate virtually concurrently.
While these combo wireless chips are key to high-performance
spectrum sharing, coexistence interfaces also pose a side-channel
risk as demonstrated by the same set of researchers at the Black Hat security conference[3] last year, effectively
permitting a malicious party to glean details from other wireless
technologies supported by the combo chip.
Dubbed “Spectra,” the vulnerability class banks on the fact that
transmissions happen in the same spectrum and wireless chips need
to arbitrate the channel access. This breaks the separation between
Wi-Fi and Bluetooth to result in denial-of-service on spectrum
access, information disclosure, and even enable lateral privilege
escalations from a Bluetooth chip to code execution on a Wi-Fi
chip.
“The Wi-Fi chip encrypts network traffic and holds the current
Wi-Fi credentials, thereby providing the attacker with further
information,” the researchers said. “Moreover, an attacker can
execute code on a Wi-Fi chip even if it is not connected to a
wireless network.”
In addition, the researchers found that it’s possible for an
adversary with control over the Wi-Fi core to observe Bluetooth
packets, which, in turn, allows determining keystroke timings on
Bluetooth keyboards, ultimately granting the attacker the ability
to reconstruct text entered using the keyboard.
While some of the attack scenarios were first reported to the
vendors as early as August 2019, the coexistence flaws continue to
remain unpatched on Broadcom SoCs to date.
“As of November 2021, more than two years after reporting the
first coexistence bug, coexistence attacks, including code
execution, still work on up-to-date Broadcom chips,” the academics
said. “This highlights how hard these issues are to fix in
practice.”
To minimize the risk of such wireless attacks, it’s recommended
that users remove unnecessary Bluetooth pairings, delete unused
Wi-Fi networks, and restrict to using cellular instead of Wi-Fi at
public spaces.
“Cellular data plans got more affordable during recent years and
cellular network coverage increased,” the researchers concluded.
“Disabling Wi-Fi by default and only enabling it when using trusted
networks can be considered a good security practice, even if
cumbersome.”
References
- ^
new
paper (arxiv.org) - ^
Coexistence
(www.silabs.com) - ^
Black
Hat security conference (www.blackhat.com)
Read more https://thehackernews.com/2021/12/researchers-uncover-new-coexistence.html