A few days ago, a friend and I were having a rather engaging
conversation that sparked my excitement. We were discussing my
prospects of becoming a red teamer as a natural career progression.
The reason I got stirred up is not that I want to change either my
job or my position, as I am a happy camper being part of Cymulate’s
blue team.
What upset me was that my friend could not grasp the idea that I
wanted to keep working as a blue teamer because, as far as he was
concerned, the only natural progression is to move to the red
team.
Red teams include many roles ranging from penetration testers to
attackers and exploit developers. These roles attract most of the
buzz, and the many certifications revolving around these roles
(OSCP, OSEP, CEH) make them seem fancy. Movies usually make hackers
the heroes, while typically ignoring the defending side, the
complexities and challenges of blue teamers’ roles are far less
known.
While blue teams’ defending roles might not sound as fancy and
gather little to no buzz, they include essential and diverse titles
that cover exciting and challenging functions and, finally, pay
well. In fact, Hollywood should look into it!
Defending is more complex than attacking, and it is more
crucial
Consider that you are a cyber security defender and that your
assigned job is to protect your IT Infrastructure.
- As a defender, you need to learn all sorts of attack mitigation
techniques to protect your IT infrastructure. Conversely, an
attacker can settle for gaining proficiency in exploiting just one
vulnerability and keep exploiting that single vulnerability. - As a defender, you must be alert 24/7/365 to protect your
infrastructure. As an attacker, you either choose a specific
time/date to launch an attack or run boring brute force attacks
across many potential targets. - As a defender, you must protect all weak links in your
infrastructure – xerox, machine printer, attendance system,
surveillance system, or endpoint used by your receptionist –
whereas attackers can select any system connected to your
infrastructure. - As a defender, you must comply with your local regulator while
performing your daily work. Attackers have the liberty to mess up
with laws and regulations. - As a defender, you are prepared by the red team that assists
your work by creating attack scenarios to test your
capabilities.
Blue teams include complex, challenging, and research-intensive
disciplines, and the related roles are not filled.
In the conversation mentioned above, my friend assumed that
defending roles mainly consist of monitoring SIEMs (Security
Information and Event Management) and other alerting tools, which
is correct for SOC (Security Operations Center) analyst roles. Here
are some atypical Blue Team roles:
- Threat Hunters – Responsible for proactively
hunting for threats within the organization - Malware Researchers – Responsible for reverse
engineering malware - Threat Intelligence Researchers – Responsible
for providing intelligence and information regarding future attacks
and attributing attacks to specific attackers - DFIR – Digital Forensics and Incident
Responders are responsible for containing and investigating attacks
when they happen
These roles are challenging, time intensive, complex, and
demanding. Additionally, they involve working together with the
rest of the blue team to provide the best value for the
organization.
According to a recent CSIS survey of IT decision makers across
eight countries: “82 percent of employers report a shortage of
cybersecurity skills, and 71 percent believe this talent gap causes
direct and measurable damage to their organizations.” According to
CyberSeek, an initiative funded by the National Initiative for
Cybersecurity Education (NICE), the United States faced a shortfall
of almost 314,000 cybersecurity professionals as of January 2019.
To put this in context, the country’s total employed cybersecurity
workforce is just 716,000. According to data derived from job
postings, the number of unfilled cybersecurity jobs has grown by
more than 50 percent since 2015. By 2022, the global cybersecurity
workforce shortage has been projected to reach upwards of 1.8
million unfilled positions.”
C Level executives are disconnected from reality when it comes
to Internal Blue Teams
The above graph is from an excellent talk called “How to Get
Promoted: Developing Metrics to Show How Threat Intel Works – SANS
CTI Summit 2019”. It illustrates the disconnect between the
high-level executives and “on-the-ground” employees and how
high-level executives think that their defensive teams are much
more mature than their team self-assessment.
Solving the Problem
Strive to teach SOC analyst’s new craft
Bringing new and experienced researchers is expensive and
complicated. Perhaps organizations should strive to promote and
encourage entry analysts to learn and experiment with new skills
and technologies. While SOC managers might fear that this might
interfere with experienced analysts’ daily missions or result in
people leaving the company but, paradoxically, it will encourage
analysts to stay and take a more active part in maturing the
organization’s security at almost no extra cost.
Cycle employees through positions
People get tired of doing the same thing every day. Perhaps a
clever way to keep employees engaged and strengthen your
organization is to let people cycle across distinct roles, for
example, by teaching threat hunters to conduct threat intelligence
work by giving them easy assignments or sending them off to
courses. Another promising idea is to involve low-tier SOC analysts
with real Incident Response teams and thus advance their skills.
Both organizations and employees benefit from such
undertakings.
Let our employees see the results of their demanding work
Whether low-tier SOC analysts or Top C-level executives, people
need motivation. Employees need to understand whether they are
doing their job well, and executives need to understand their job’s
value and the quality of its execution.
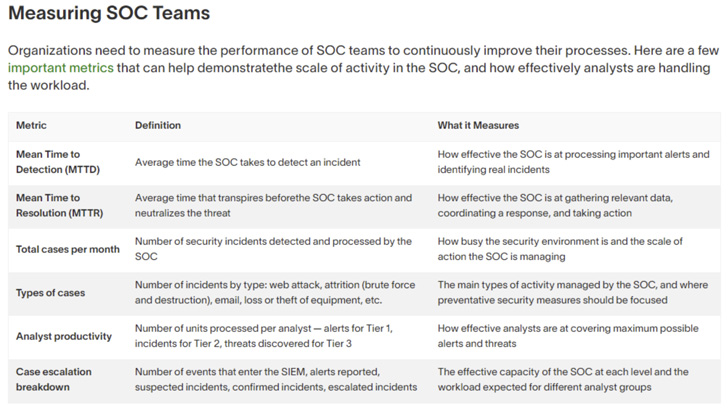
Consider ways to measure your Security Operations Center:
- How effective is the SOC at processing important alerts?
- How effectively is the SOC gathering relevant data,
coordinating a response, and taking action? - How busy is the security environment, and what is the scale of
activities managed by the SOC? - How effectively are analysts covering the maximum possible
number of alerts and threats? - How adequate is the SOC capacity at each level, and how heavy
is the workload for different analyst groups?
The table below contains more examples and measures taken from
Exabeam.
And, of course, validate your blue team’s work with continuous
security validation tools such as those on Cymulate’s XSPM platform
where you can automate, customize and scale up attack scenarios and
campaigns for a variety of security assessments.[1]
Seriously, validating your blue team’s work both increases your
organization’s cyber resilience and provides quantified measures of
your blue team’s effectiveness across time.
Note: This article is written and contributed by by Dan
Lisichkin, Threat Hunter and Threat Intelligence Researcher at
Cymulate[2].
References
Read more https://thehackernews.com/2022/08/the-benefits-of-building-mature-and.html