to be behind a sustained cyber espionage campaign targeting
government entities in Australia, Indonesia, Philippines, Vietnam,
Thailand, Myanmar, and Brunei—which went undetected for at least
five years and is still an ongoing threat.
The group, named ‘Naikon APT,’ once known as one of the most
active APTs in Asia until 2015, carried out a string of
cyberattacks in the Asia-Pacific (APAC) region in search of
geopolitical intelligence.
According to the latest investigation report Check Point
researchers shared with The Hacker News, the Naikon APT group had
not gone silent for the last 5 years, as initially suspected;
instead, it was using a new backdoor, called “Aria-body,” to
operate stealthily.
“Given the characteristics of the victims and capabilities
presented by the group, it is evident that the group’s purpose is
to gather intelligence and spy on the countries whose governments
it has targeted,” the researchers said.
In brief, the Aria-body backdoor is being used to take control of
the internal networks of a targeted organization, in addition to
mounting attacks from an already breached company to infect
another.
“This includes not only locating and collecting specific
documents from infected computers and networks within government
departments, but also extracting removable data drives, taking
screenshots and keylogging, and of course, harvesting the stolen
data for espionage.”
A Geo-Political Intelligence Campaign
First documented[1] in 2015, the Naikon APT
group uses crafted email lures as an initial attack vector against
top-level government agencies and civil and military organizations,
which, when opened, installed spyware that exfiltrated sensitive
documents to remote command-and-control (C2) servers.
Although no new signs of activity have been reported since then,
Check Point’s latest research casts its operations in a fresh
light.
“Naikon attempted to attack one of our customers by
impersonating a foreign government – that’s when they came back
onto our radar after a five-year absence, and we decided to
investigate further,” Lotem Finkelsteen, manager of threat
intelligence at Check Point, said.
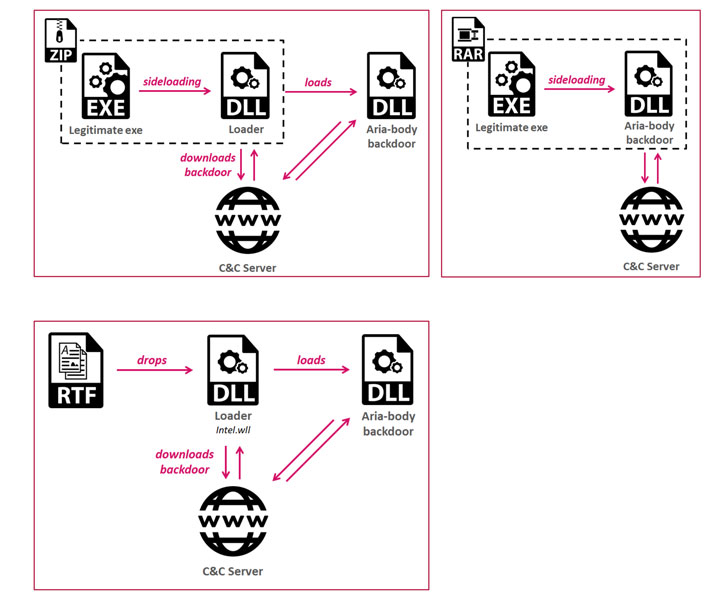
Not only were multiple infection chains employed to deliver the
Aria-body backdoor, but the malicious emails also contained an RTF
file (named “The Indians Way.doc”) that was infected with an
exploit builder called RoyalBlood, which dropped a loader
(intel.wll) in the system’s Microsoft Word startup folder
(“%APPDATA%\Microsoft\Word\STARTUP”).
shared mostly among Chinese threat actors. It’s worth noting that a
similar modus operandi has been linked to a campaign against
Mongolian government agencies, called Vicious
Panda[3], that was found
exploiting the ongoing coronavirus outbreak to plant malware via
social engineering tricks.
In a separate infection mechanism, archive files were packaged
with a legitimate executable (such as Outlook and Avast Proxy) and
a malicious library to drop the loader on the target system.
Regardless of the method to gain an initial foothold, the loader
then established a connection with a C2 server to download the
next-stage Aria-body backdoor payload.
“After getting the C&C domain, the loader contacts it to
download the next and final stage of the infection chain,” the
researchers noted. “Although it sounds simple, the attackers
operate the C&C server in a limited daily window, going online
only for a few hours each day, making it harder to gain access to
the advanced parts of the infection chain.”
The Aria-body RAT, named so based on the name
“aria-body-dllX86.dll” given by the malware authors, has all the
features you’d expect from a typical backdoor: create and delete
files and directories, take screenshots, search for files, gather
file metadata, collect system and location information, among
others.
Some recent variations of Aria-body also come equipped with
capabilities to capture keystrokes, and even load other extensions,
per researchers, suggesting the backdoor is under active
development.
Aside from exfiltrating all the gathered data to the C2 server,
the backdoor listens for any additional commands to be
executed.
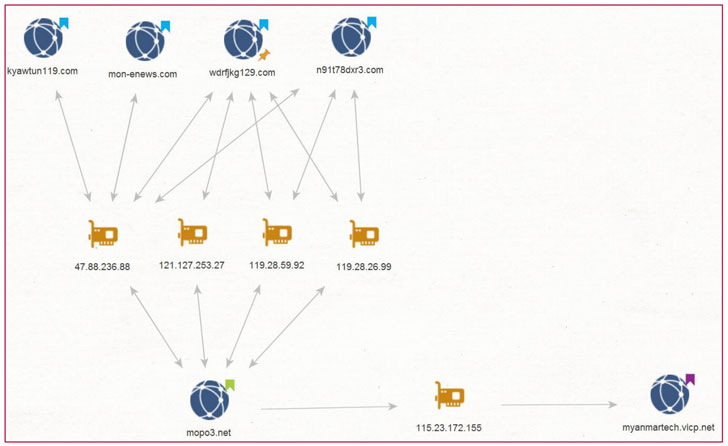
Further analysis of the C2 infrastructure found that several
domains were used for long stretches of time, with the same IP
address reused with more than one domain.
Taking their evasion tactics to the next level, the adversary
compromised and used servers within the infected ministries as C2
servers to launch attacks, and relay and route the stolen data,
rather than risk detection when accessing the remote servers.
Ties to Naikon APT
Check Point said it attributed the campaign to the Naikon APT based
on code similarities in Aria-body and the espionage tool detailed by
Kaspersky[4] (called “XSControl”) in
2015, as well as in the use of C2 domains (mopo3[.]net) that
resolve to the same IP address as the domains mentioned by the
latter (myanmartech.vicp[.]net).
years, it appears that they have not been idle,” Check Point
concluded. “In fact, quite the opposite. By utilizing new server
infrastructure, ever-changing loader variants, in-memory fileless
loading, as well as a new backdoor — the Naikon APT group was able
to prevent analysts from tracing their activity back to
them.”
References
- ^
documented
(securelist.com) - ^
RoyalBlood
(blog.malwarelab.pl) - ^
Vicious Panda
(research.checkpoint.com) - ^
detailed by Kaspersky
(securelist.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/3mdfxlhuBic/asia-pacific-cyber-espionage.html