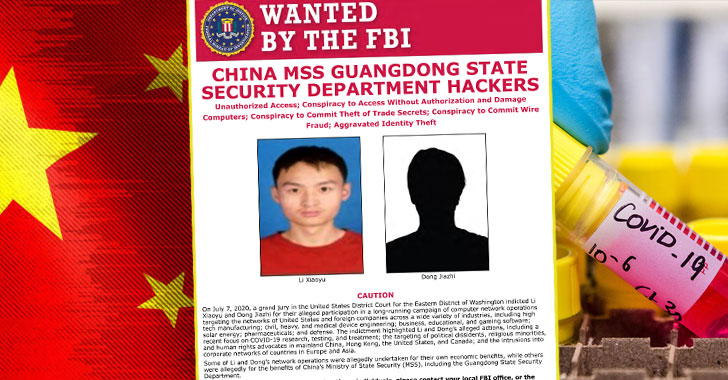
charges against two Chinese nationals for their alleged involvement
in a decade-long hacking spree targeting dissidents, government
agencies, and hundreds of organizations in as many as 11 countries.
The 11-count indictment[1], which was unsealed on
Tuesday, alleges LI Xiaoyu (李啸宇) and DONG Jiazhi (董家志) stole
terabytes of sensitive data, including from companies developing
COVID-19 vaccines, testing technology, and treatments while
operating both for private financial gain and behalf of China’s
Ministry of State Security.
“China has now taken its place, alongside Russia, Iran and North
Korea, in that shameful club of nations that provide a safe haven
for cyber criminals in exchange for those criminals being ‘on call’
to work for the benefit of the state, [and] to feed the Chinese
Communist party’s insatiable hunger for American and other
non-Chinese companies’ hard-earned intellectual property, including
COVID-19 research,” said Assistant Attorney General John C. Demers,
who leads the DoJ’s National Security Division.
The pair, who are currently
wanted by the U.S. Federal Bureau of Investigation, came under
the radar after they compromised a U.S. Department of Energy
network in Hanford, which is home to a decommissioned nuclear
production complex located in the state of Washington.
Aside from this breach, the individuals in questions have been
accused of infiltrating the networks of companies spanning high
tech manufacturing, industrial engineering, defense, educational,
gaming software, and pharmaceutical sectors with an aim to steal
trade secrets and other confidential business information.
Besides the U.S., a number of victim organizations are based in
Australia, Belgium, Germany, Japan, Lithuania, the Netherlands,
Spain, South Korea, Sweden, and the U.K. In all, the targeted
cyberattacks lasted over a period of more than ten years, starting
around September 1, 2009, and continuing through July 7, 2020, the
DoJ said.
Exploiting Unpatched Vulnerabilities in Web Applications
According to the indictment, the hackers gained an initial
foothold to the companies by exploiting insecure default
configurations or freshly disclosed security flaws in popular
software that hadn’t yet been patched.
The two suspects, then, installed credential-stealing software
to gain deeper access and leveraged web shells to execute malicious
programs, and transfer the data in the form of compressed RAR
files, but not before changing their extensions to “.JPG” to mask
the exfiltration process in the form of innocuous images.
The stolen data, which ran into hundreds of gigabytes, consisted
of source code, information about drugs under active development,
weapon designs, and personally identifiable information, the DoJ
noted.
What’s more, all the malicious activities were performed on the
Recycle Bin of the targeted Windows systems, using it to load the
executables into specific folders and save the RAR files.
“In at least one instance, the hackers sought to extort
cryptocurrency from a victim entity, by threatening to release the
victim’s stolen source code on the Internet,” the DoJ said. “More
recently, the defendants probed for vulnerabilities in computer
networks of companies developing COVID-19 vaccines, testing
technology, and treatments.”
It’s Not Just China
The development is all the more significant since it comes just
months after both the FBI and Homeland Security warned that China
was actively trying to steal
data[3] from organizations
working on COVID-19 research and amid mounting tensions between the
U.S. and China over national security concerns.
But China isn’t the only nation that’s been accused of using its
offensive cyber capabilities to steal coronavirus research.
In May, Iran-backed
hackers[4] purportedly targeted
U.S. drugmaker Gilead, whose antiviral drug remdesivir has been
proven to trigger an immune response in patients infected with
COVID-19.
Then last week, the U.K.’s National Cyber Security Centre (NCSC)
alleged that hackers[5] linked to Russian
intelligence[6] services (APT29 or
CozyBear) had targeted companies researching a coronavirus vaccine
in the U.S., U.K., and Canada without specifying which
organizations had been targeted, or whether any information had
been stolen. Russia has denied[7] the allegations.
Li and Dong are charged with identity theft, conspiracy to
commit wire fraud, theft of trade secrets, and violating
anti-hacking laws, all of which collectively carry a maximum
sentence of over 40 years.
References
- ^
indictment
(www.justice.gov) - ^
currently wanted
(www.justice.gov) - ^
steal data
(www.fbi.gov) - ^
Iran-backed hackers
(www.reuters.com) - ^
hackers
(www.nsa.gov) - ^
Russian intelligence
(www.ncsc.gov.uk) - ^
denied
(www.bbc.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/EXugG_mFt0A/chinese-hackers-covid19.html